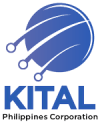
Compromising a single workstation on a flat enterprise network gives an attacker direct Layer 2 adjacency to every SIP trunk, call manager, and video bridge in the building. No pivoting required, no firewall to bypass, no privilege escalation needed. The attacker is already there, in the same broadcast domain as your voice and collaboration infrastructure, free to sniff RTP streams, spoof caller IDs, or hijack active sessions.
This is the core architectural problem that sinks enterprise unified communications deployments. And it’s alarmingly common: a 2026 survey of 400 U.S. network security practitioners found that only one-third of organizations have fully implemented both macro- and micro-segmentation. Everyone else runs with partial controls or none at all. For Philippine enterprises operating BPO contact centers with thousands of concurrent calls, hospitals handling sensitive patient communications, or government agencies bound by NTC and DICT mandates, that gap represents real exposure.
An infrastructure-first UC adoption approach treats segmentation as the prerequisite for everything else. Not the finishing touch. Not the hardening step you’ll get to after rollout. The prerequisite.
Why Flat Networks and UC Are Incompatible
Traditional enterprise LANs were designed for convenience. Plug in a device, get an IP, reach everything. That model worked tolerably when the network carried email and file shares. It collapses when you add real-time media.
UC systems depend on a constellation of services: SIP registrars, media gateways, SRTP key exchanges, presence servers, voicemail stores, and directory integrations. Each of these components trusts the network to deliver traffic from authenticated peers. On a flat network, every compromised endpoint looks like an authenticated peer. An attacker who lands on any machine in the subnet can send SIP INVITE packets directly to your PBX, register rogue extensions, or intercept unencrypted RTP streams.
The problem gets worse with IoT and smart devices. Conference room displays, IP cameras, and door access controllers all live on the same flat network in many Philippine offices. Each one is a potential entry point. Once inside, lateral movement to UC infrastructure is trivial.
If you’ve experienced unexplained call quality degradation or network congestion, a flat architecture may be contributing. Broadcast storms and rogue traffic from compromised endpoints eat into the jitter and latency budgets that voice depends on.
VLANs Are the Starting Point
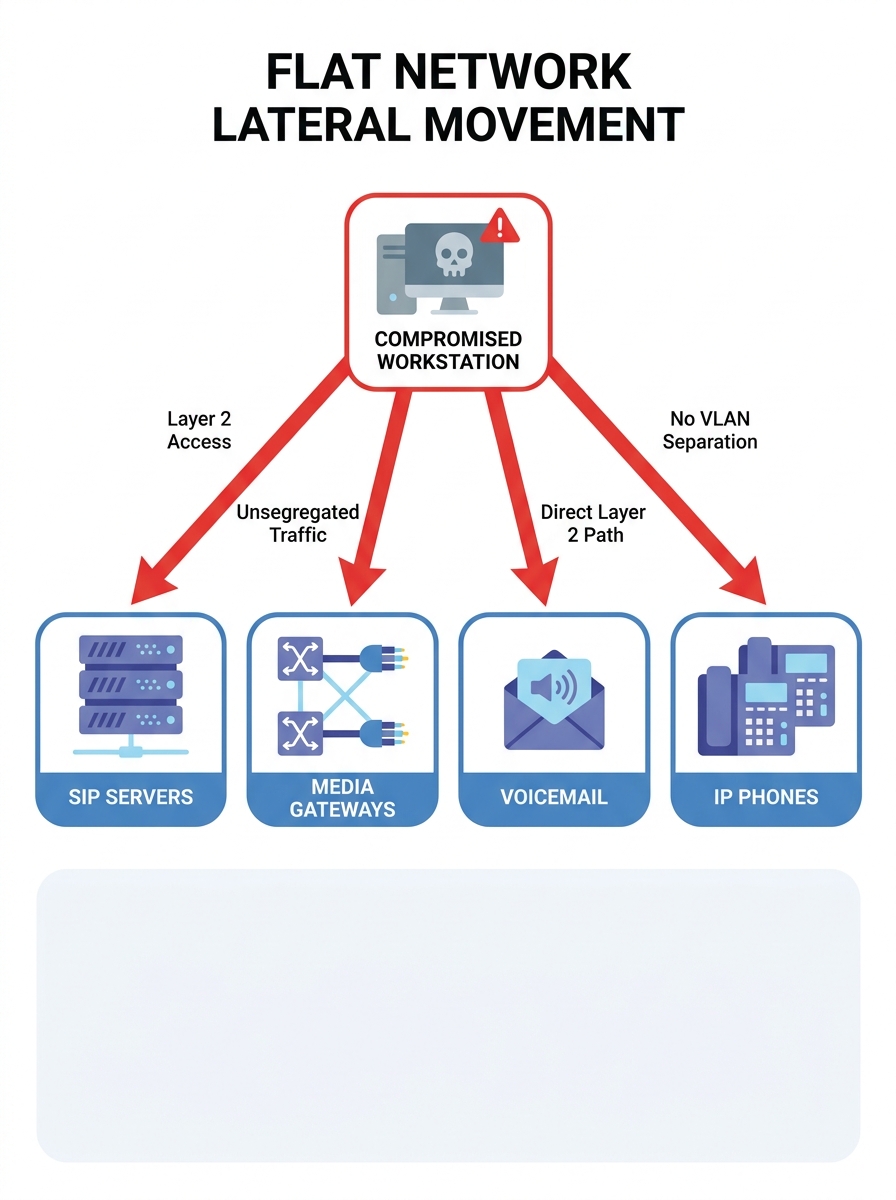
Cisco Press recommends logical segmentation through virtual LANs as the baseline best practice for UC environments. A properly designed VLAN scheme separates voice endpoints, UC servers, user workstations, and management interfaces into distinct broadcast domains. Inter-VLAN routing is then controlled by firewall rules or Layer 3 ACLs that permit only the specific traffic flows UC requires.
A typical enterprise VoIP architecture in a Philippine BPO operation might look like this:
- Voice VLAN for IP phones (Fanvil, Yeastar, or Cisco endpoints)
- UC Server VLAN for PBX, voicemail, and conferencing servers
- Agent Workstation VLAN for desktop PCs running softphones and CRM integrations
- Management VLAN for switch administration, jump boxes, and monitoring tools
- Guest/IoT VLAN for lobby Wi-Fi, cameras, and building systems
But VLANs alone aren’t enough. The five most common segmentation failures documented by security practitioners include creating VLANs with unrestricted inter-VLAN routing, failing to segment Wi-Fi from wired networks, placing admin accounts in user segments, allowing firewall rule sprawl, and skipping penetration testing. Every one of these turns a well-intentioned VLAN design into a false sense of security.
The fix is explicit: every inter-VLAN path should pass through a firewall or next-generation firewall (Fortinet FortiGate is popular in Philippine enterprise deployments), with rules that permit only documented traffic flows. If your voice VLAN needs to reach the SIP registrar on port 5060/5061, that rule exists. Everything else is denied by default.
Warning: Creating VLANs without firewall filtering between them is one of the most common segmentation mistakes. If inter-VLAN routing is unrestricted, you’ve added administrative complexity without gaining any security.
Micro-Segmentation for Real-Time Media
VLANs handle macro-segmentation: big zones with broad policies. Micro-segmentation goes further by enforcing policies at the individual workload or application level. According to Coeo Solutions, micro-segmentation in UC architecture restricts lateral communications in the DMZ and data centers, preventing traffic from reaching locations that may not be properly secured.
For UC, micro-segmentation means your SIP registrar can talk to your media gateway but cannot be reached by your HR file server, even if both sit in the same data center VLAN. Cisco’s TrustSec approach uses Security Group Tags (SGTs) to classify traffic by endpoint identity and context rather than IP address, which is valuable when IP assignments are dynamic or when endpoints move between locations.
In practical terms for Philippine deployments, this matters most in three scenarios:
- Multi-site BPO operations where agents in Cebu, Davao, and Metro Manila connect to centralized UC servers. Each site’s agent VLAN should only reach the specific UC services it needs, not the entire data center.
- Hospital campuses where nurse stations, doctor consult rooms, and administrative offices share physical cabling but require different access policies for patient-facing communication systems.
- Government agencies deploying VoIP under DICT guidelines, where compliance mandates that classified and unclassified communication traffic stay isolated.
If your organization maintains enterprise data center infrastructure that hosts UC workloads alongside other applications, micro-segmentation prevents a breach in one application from cascading into your communications platform.
The UCaaS Wrinkle: Segmentation in Hybrid Deployments
A growing number of Philippine enterprises are adopting cloud-based UC, either pure UCaaS or hybrid models with on-premise PBX systems connecting to cloud collaboration tools. This changes the segmentation calculus.
With on-premise UC, you control every network path. With UCaaS, your traffic traverses the public internet to reach a provider’s data center. Your UCaaS deployment strategy needs to account for where segmentation is still your responsibility and where it shifts to the provider.
Single-tenant UCaaS architectures give you a dedicated software platform where you maintain control of data residency, security policies, and integrations. As IR’s guide to UCaaS notes, this model is common in highly regulated industries like healthcare and government. Multi-tenant architectures reduce cost but require you to trust the provider’s segmentation.
Regardless of model, your internal network still needs segmentation. UCaaS doesn’t eliminate the need for local voice VLANs, QoS policies, and firewall rules. Your IP phones and softphones still generate local traffic that must be prioritized and isolated. The cloud handles the application layer; your network handles the transport layer. When you configure QoS for VoIP traffic, those DSCP markings and queue policies depend on the traffic being properly segmented first. QoS on a flat network is like painting lane markers on a road with no barriers.
QoS on a flat network is like painting lane markers on a road with no barriers. The markings exist, but nothing stops traffic from ignoring them.
Encryption and Segmentation Are Complementary
Some IT teams argue that SRTP and TLS encryption make segmentation unnecessary. If the media and signaling are encrypted, who cares if an attacker can see the packets?
This reasoning has two holes. First, encryption protects confidentiality but not availability. An attacker on the same network segment can still flood your SIP registrar with garbage traffic, conduct a denial-of-service attack against your media gateway, or exhaust bandwidth on the voice VLAN. Segmentation limits who can send traffic to those systems in the first place.
Second, encryption metadata leaks. Even with SRTP, an attacker on the same segment can observe call patterns: who is calling whom, at what times, for how long. In a BPO environment handling financial services or healthcare accounts, that metadata can be as sensitive as the call content itself. Our earlier piece on securing VoIP networks against real-world attacks details how attackers exploit these patterns.
The right approach uses both. TLS for SIP signaling, SRTP for media streams, and IPSec tunnels for site-to-site VoIP connections between remote offices, all layered on top of a segmented network that restricts which devices can even initiate those connections.
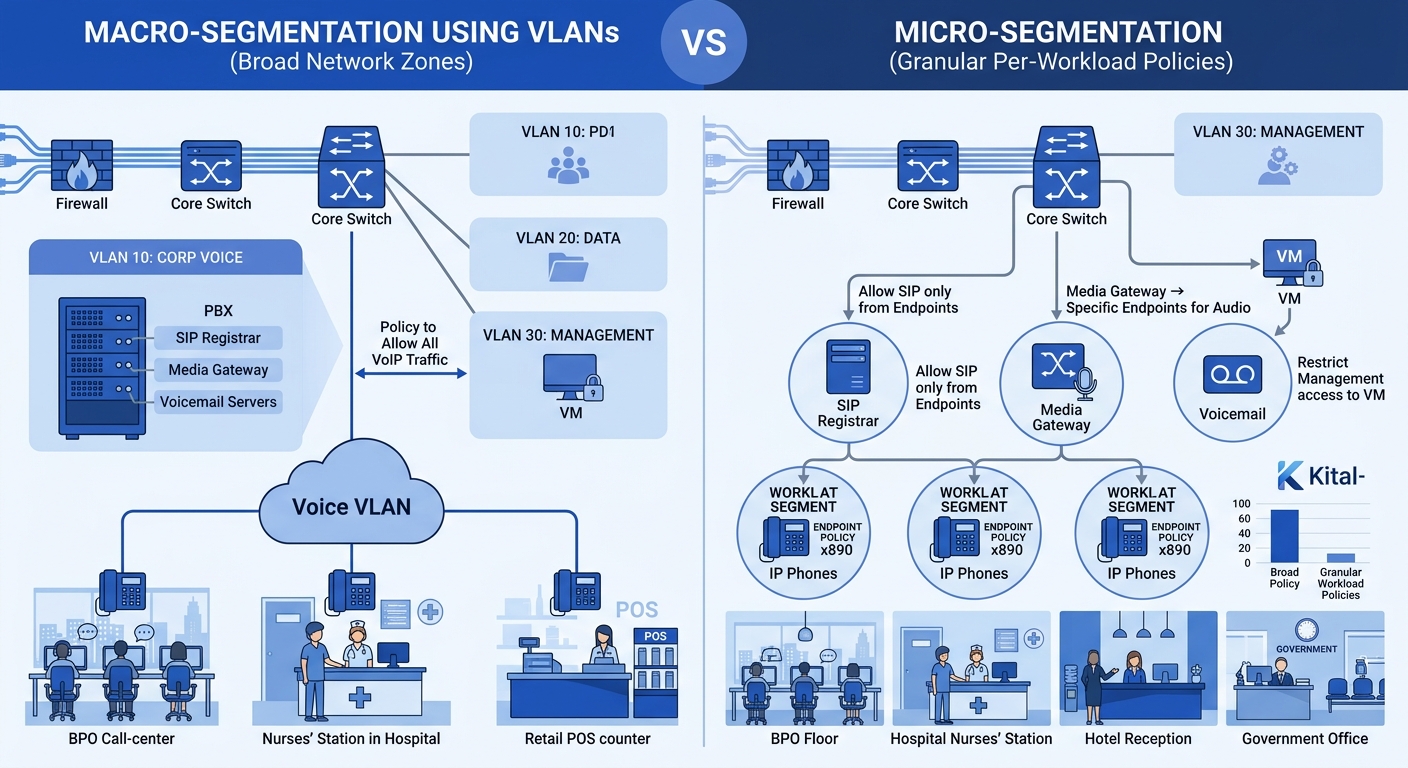
Compliance Pressures in Philippine Verticals
Philippine enterprises face a patchwork of compliance requirements that implicitly or explicitly mandate segmentation.
Financial services companies processing card payments must comply with PCI DSS, which requires network segmentation to isolate cardholder data environments. If your BPO agents take credit card numbers over VoIP calls, the call recording servers and the network paths carrying that audio fall within PCI scope. Segmentation shrinks the scope boundary and reduces the compliance burden.
Healthcare organizations operating under Philippine data privacy laws (and international standards like ISO/IEC 27001 for clients abroad) need to ensure that patient communication data stays isolated. Government agencies deploying VoIP systems face DICT cybersecurity guidelines that align with NIST frameworks, where segmentation is a core control. We’ve covered the specific requirements in our VoIP deployment checklist for Philippine government agencies.
And then there’s the practical reality: NTC spectrum and network regulations mean that many Philippine enterprises run a patchwork of ISP connections, PLDT fiber, Globe circuits, and backup LTE links. Each ingress point is a potential attack surface. Segmentation ensures that a compromise on one circuit doesn’t give access to UC systems reachable from another.
Building the Segmentation Plan Before the UC Rollout
The sequence matters. Too many Philippine IT teams deploy Yeastar or Cisco Unified Communications Manager first, confirm that calls work, and then try to retrofit segmentation. This approach creates pain. Retrofitting means re-IPing phones, restructuring switch port assignments, and rewriting firewall rules while the system is in production. Users notice. Management complains. The segmentation project stalls at 60% completion.
The better sequence:
- Map your UC traffic flows before purchasing hardware. Document every communication path: phone to PBX, PBX to PSTN gateway, softphone to SIP proxy, recording server to storage, management workstation to UC admin interface.
- Design VLAN and subnet architecture around those flows. Assign dedicated VLANs for voice endpoints, UC servers, management, and any IoT devices that interact with the communications system.
- Deploy firewall rules between every segment. Start with deny-all and whitelist specific flows. This is tedious and requires discipline, but it’s the only approach that works.
- Install and configure UC components into the pre-built segments. Phones land in the voice VLAN from day one. Servers land in the UC server VLAN from day one. No temporary flat-network phase.
- Test lateral movement with a penetration test focused on east-west traffic. Can you reach the PBX from the guest Wi-Fi? Can a compromised agent workstation enumerate UC management interfaces?
Microsoft’s Azure Well-Architected Framework acknowledges the complexity tradeoff: segmentation introduces overhead in management and cost, since more resources are provisioned when environments are segmented. But the alternative is accepting that any breach anywhere on your network becomes a breach of your entire communications platform.
What Still Isn’t Settled
Several open questions remain for Philippine enterprises pursuing unified communications security through segmentation.
The tooling gap is real. Micro-segmentation products from vendors like Cisco (TrustSec/ISE), Fortinet (FortiNAC), and cloud-native tools assume a level of asset visibility that many Philippine networks don’t have. If you can’t inventory every device on your network accurately, you can’t write micro-segmentation policies for them. The 2026 practitioner survey identified this as a core failure mode, calling it the “Scope & Visibility Trap,” where organizations attempt segmentation without adequate asset discovery and stall out.
There’s also tension between segmentation and user experience. UC platforms promise seamless collaboration anywhere, on any device. Aggressive segmentation can block legitimate flows if policies aren’t carefully maintained. Bring-your-own-device policies common in Philippine companies add complexity; a personal laptop joining the corporate Wi-Fi shouldn’t reach the voice VLAN, but a company-issued softphone on that same laptop needs to.
And the skills question looms large. Designing and maintaining segmented UC networks requires networking and security expertise that’s in short supply in the Philippine IT labor market. Managed service providers can fill the gap, but the enterprise still needs internal staff who understand the architecture well enough to troubleshoot when calls drop because a firewall rule was too restrictive.
The organizations getting this right share a common trait: they treat network segmentation UC design as a precondition for communications deployment, not a hardening exercise to schedule later. The gap between those organizations and the two-thirds still running flat or partially segmented networks will continue to widen as UC attack surfaces grow with every new integration, endpoint type, and cloud service added to the mix.