CVE-2026-2329 gave attackers unauthenticated root-level access to Grandstream IP phones, letting them intercept calls, commit toll fraud, and impersonate users across an entire SMB phone system. No password required. The vulnerability, documented by Dark Reading, affected devices sitting in lobbies, nursing stations, and front desks of businesses across Southeast Asia, including the Philippines. If your organization runs VoIP, the real question isn’t whether to invest in security. It’s where to invest first.
Three broad strategies dominate the conversation around VoIP security vulnerabilities and telecom breach prevention: locking down the network perimeter, hardening endpoints and protocols at the device level, or investing in real-time monitoring and automated response. Each carries real tradeoffs in cost, complexity, and the types of attacks it actually stops. Here’s how they stack up against each other.
Perimeter-First Defense: Firewalls, SBCs, and VLANs
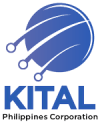
The perimeter approach treats your VoIP infrastructure the way a gated compound treats its walls. You segment voice traffic onto its own VLAN, deploy a Session Border Controller (SBC) at every trunk interconnect, and configure your firewall rules to allow only the SIP and RTP ports your system actually needs. Everything else gets dropped.
This strategy is effective against the most common class of VoIP attacks: reconnaissance scans, brute-force SIP registration attempts, and volumetric denial-of-service floods. A Fortinet or Cisco firewall configured with SIP-aware application layer gateways can inspect signaling traffic and reject malformed packets before they reach your IP PBX. Network segmentation also limits blast radius. If ransomware hits a workstation on your data VLAN, your voice infrastructure stays isolated.
The tradeoff? Perimeter defenses do almost nothing against insider threats, compromised credentials, or supply chain attacks like the 3CX incident of 2023. They also require careful maintenance. Misconfigured NAT traversal rules are among the most persistent network headaches in Philippine deployments, especially when SIP trunks cross between on-premise PBXes and cloud-hosted systems. A single overly permissive firewall rule can undo months of hardening work.
For BPO call centers in Metro Manila or Cebu running hundreds of concurrent SIP sessions, perimeter defense is table stakes. You can’t skip it. But treating it as your entire security strategy leaves significant gaps, particularly around SIP protocol threats that arrive inside legitimate-looking traffic.
Where perimeter defense fits best
Organizations with flat networks and no segmentation at all get the biggest immediate risk reduction from this approach. If you’re choosing a new business telephone system for an office build-out, designing VLANs into the network from day one costs almost nothing compared to retrofitting later. Pairing your PBX deployment with proper network security solutions at the design stage prevents the kind of patchwork configurations that attackers love to exploit.
Hardening the Endpoints and Protocols Themselves
The second approach focuses inward: locking down the SIP protocol implementation, the PBX configuration, and the physical and logical settings on every IP phone and gateway in your environment.
IP PBX hardening starts with the basics. Change default admin passwords on your Yeastar or Asterisk-based system. Disable unused SIP extensions. Enforce TLS for SIP signaling and SRTP for media encryption. Require strong authentication on every trunk registration. These steps sound obvious, but CVE-2026-2329 exploited exactly this kind of oversight on devices where factory defaults were never changed.
SIP protocol threats go deeper than brute-force registration attempts. Researchers at Claroty’s Team82 demonstrated that a single malformed SIP URI could crash client applications through a null pointer dereference, affecting everything from desk phones to IoT doorbells that use VoIP for audio. Meanwhile, security researchers documented how attackers could abuse SIP User-Agent headers to trigger cross-site scripting attacks in call monitoring dashboards. The SIP protocol was designed in the late 1990s without security as a core priority, and it carries inherent risks that perimeter controls alone cannot address.
Warning: Attackers can create fake IP packets using your organization’s IP address and impersonate your SIP devices, making unauthorized calls that appear to originate from your system. Enforcing digest authentication and TLS on all SIP registrations blocks this class of attack.
Endpoint hardening also means firmware discipline. Fanvil, Yeastar, and Grandstream all publish regular firmware updates that patch known VoIP security vulnerabilities. Organizations that maintain current firmware see measurably fewer successful attacks, yet firmware updates remain one of the most neglected maintenance tasks in Philippine IT departments. The tendency to “set it and forget it” after a phone system deployment is a real operational risk. Building business continuity plans that account for regular patching cycles is one of the most effective things a mid-sized organization can do.
A VoIP phone left on factory default credentials is an open door. The attacker doesn’t need to pick the lock when you’ve left the key taped to the frame.
Where endpoint hardening fits best
Hospitals, schools, and government agencies with diverse device fleets benefit most here. A provincial government office might run a mix of Fanvil desk phones, softphone apps on staff laptops, and analog gateways for legacy fax machines. Each device type needs its own hardening checklist. If your organization handles patient data, compliance requirements around critical infrastructure cybersecurity make endpoint-level encryption and access controls mandatory.
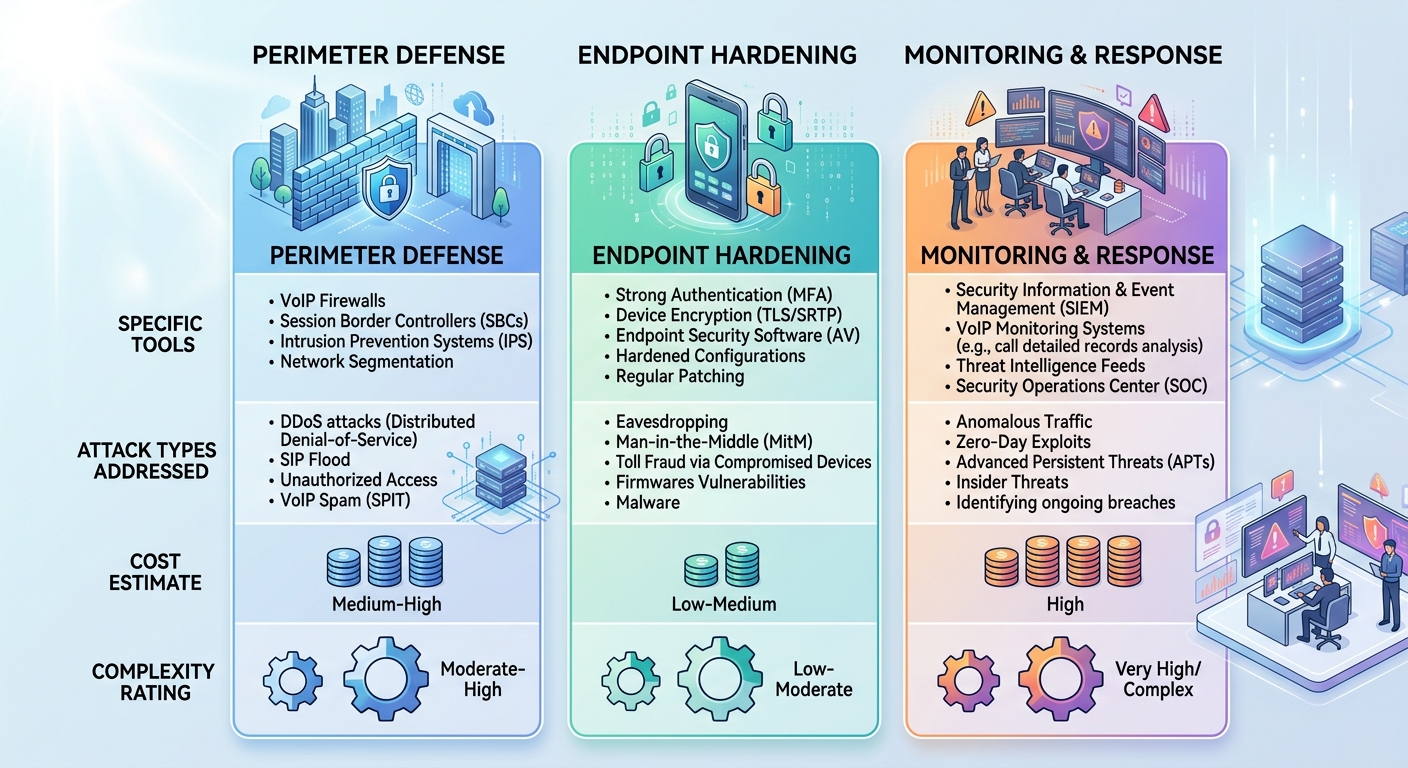
Real-Time Monitoring and Automated Response
The third strategy assumes that breaches will happen and focuses on detecting and containing them fast. This is where tools like Fail2Ban, intrusion detection systems (IDS), and call detail record (CDR) analysis come into play.
Fail2Ban monitors your PBX logs for patterns like repeated failed SIP registration attempts from a single IP address, then automatically updates your firewall to block that source. It’s built into many Yeastar and open-source PBX platforms, and it stops brute-force attacks cold. But Fail2Ban is reactive by design. It catches known-bad patterns. It won’t flag a compromised credential being used to make legitimate-looking international calls at 3 AM on a Sunday.
That’s where CDR anomaly detection matters. If your Davao office typically handles 200 calls per day and your system suddenly routes 2,000 calls to premium-rate numbers in Eastern Europe over a weekend, an anomaly detection system flags the spike and can auto-disable the affected trunk or extension. Toll fraud remains one of the most financially damaging VoIP attacks in the Philippines, with some BPOs reporting six-figure losses from a single compromised trunk over a holiday weekend.
Network-level IDS/IPS solutions from Fortinet or Cisco can inspect SIP and RTP traffic in real time, looking for signatures of known exploits and behavioral anomalies. These tools provide visibility into attack patterns that would be invisible at the endpoint or perimeter layer alone. They’re also where unified communication platforms with built-in security dashboards can consolidate alerts and triage them before they reach your already-stretched IT team.
The tradeoff with monitoring is operational overhead. Someone has to read the alerts. A hospital IT team of three people managing 500 IP phones, the campus Wi-Fi, and the EHR system doesn’t have the bandwidth to investigate every Fail2Ban trigger. False positives erode trust in the alerting system, and eventually alerts get ignored entirely. Organizations in this position should consider managed security service providers (MSSPs) that specialize in voice network monitoring, or at minimum, set up automated escalation rules that filter noise and surface only high-confidence incidents.

Where monitoring fits best
Organizations that have already implemented perimeter and endpoint controls but want earlier detection of sophisticated attacks. It’s also critical for businesses with remote workers or distributed offices across Luzon, Visayas, and Mindanao, where VoIP traffic traverses the public internet and the attack surface is wider. If you’ve previously troubleshot VoIP quality and connectivity issues, you already know that visibility into what’s happening on your voice network is half the battle. Monitoring takes that visibility and turns it into a defensive capability.
How To Choose Between These Three
The honest answer: you need all three, and you probably can’t afford to implement all three at full maturity simultaneously. So the question becomes one of sequencing.
If you’re a small business with under 50 extensions and a single site, start with perimeter defense and endpoint hardening together. Segment your VoIP traffic, change every default password, enable TLS and SRTP, and configure Fail2Ban. That combination blocks the vast majority of opportunistic attacks, which are the type most likely to hit a small Philippine business.
If you’re a mid-sized BPO, hospital, or university with 200+ extensions across multiple locations, perimeter and endpoint controls are prerequisites, and real-time monitoring becomes essential. Toll fraud detection and CDR anomaly alerting should be running within the first quarter of any new deployment.
If you’re a government agency or critical infrastructure operator subject to DICT or NTC compliance requirements, all three layers need formal policies, documented procedures, and regular penetration testing. Refresher training for staff, scheduled password rotations, and periodic security audits aren’t optional extras. They’re the difference between a contained incident and a breach that makes the evening news.
The attacks documented in CVE-2026-2329, the Claroty SIP research, and the 3CX supply chain compromise share a common lesson. The organizations that suffered the worst consequences weren’t using exotic technology. They were running the same VoIP platforms as everyone else but had skipped basic hygiene in at least one of these three defensive layers. Whichever layer you strengthen first, make sure none of the three stays at zero.