Every Philippine government agency deploying VoIP must hold a valid Certificate of Registration (COR) from the National Telecommunications Commission, renewed annually at PhP 5,000, before a single IP phone powers on. NTC Memorandum Order No. 3-11-2005 spells this out, and the application form itself classifies VoIP under Value-Added Service (VAS) providers. Agencies that skip or delay this registration expose themselves to administrative penalties, service shutdowns, and audit findings from the Commission on Audit.
That registration requirement shapes everything downstream. It determines which vendors you can contract, which interconnection fees apply (PhP 1.00 per call to fixed lines, PhP 1.50 for calls terminating on mobile networks), and how your traffic is classified on the public switched telephone network. If your agency can’t show a current COR during an NTC spot audit, the entire phone system is operating illegally. The compliance burden falls on the agency, not on the vendor who sold you the hardware.
This checklist walks through the three pillars of a defensible VoIP government deployment: Philippine NTC compliance, secure VoIP implementation, and network QoS for government infrastructure.
NTC Registration and the Philippine Regulatory Framework
Republic Act No. 7925, the Public Telecommunications Policy Act, provides the statutory backbone for VoIP regulation in the Philippines. The NTC issued Memorandum Circular No. 05-08-2005 to establish specific rules governing VoIP services, and two provisions matter most for government agencies.
Section 7 of that circular prohibits internet service providers from bundling conditions onto broadband subscribers. In practical terms, your ISP cannot require your agency to purchase a specific IP-enabled service or block you from using a third-party VoIP platform. If a vendor or ISP tells you otherwise, cite the circular directly.
Section 8 governs the sale, lease, importation, and distribution of VoIP equipment. Any IP phone, VoIP gateway, or SIP trunk adapter your agency procures should carry NTC type-approval. Fanvil and Yeastar devices sold through authorized Philippine distributors generally come with this approval already in hand, but surplus or gray-market equipment often does not. Verify type-approval before issuing a purchase order.
Data Privacy Act Obligations
VoIP systems capture and store personal data: caller IDs, call recordings, voicemail content, directory information. Under RA 10173 (the Data Privacy Act of 2012), your agency must conduct a Privacy Impact Assessment before deployment. The National Privacy Commission requires agencies to appoint a Data Protection Officer, set retention limits on call records, and report breaches within 72 hours of discovery.
Call recordings deserve special attention. If your agency records calls for quality assurance or legal compliance, those recordings become part of your system of records. You need documented policies on who can access them, how long they’re retained, and under what conditions they’re destroyed.

The Security Checklist for Government VoIP
Government voice traffic is a high-value target. Call interception, toll fraud, caller ID spoofing, and denial-of-service attacks all exploit weaknesses specific to IP-based telephony. NIST Special Publication 800-58 remains the most referenced framework for VoIP security planning, and its recommendations translate well to Philippine agency environments.
Here’s what your VoIP security checklist should include:
Encryption and Protocol Selection
- SIP over TLS for all signaling traffic. Standard SIP transmits call setup information in plaintext, meaning anyone with packet-capture access on your LAN can see who’s calling whom.
- SRTP (Secure Real-time Transport Protocol) for media encryption. Without SRTP, the actual voice audio is vulnerable to interception.
- If your agency handles classified or restricted information, consider FIPS 140-2 validated encryption modules. The U.S. Department of Homeland Security mandates FIPS 140-2 for all sensitive voice communications on federal networks, and Philippine agencies working with foreign partners on defense or intelligence matters should match that standard.
Network Segmentation and Access Control
Separate your VoIP VLAN from your data VLAN. This is non-negotiable. When voice and data traffic share the same broadcast domain, a compromised workstation can be used to sniff voice packets, launch ARP cache poisoning attacks, or flood the network with enough traffic to degrade call quality.
Disable unused switch ports in wiring closets. In a government building, unused Ethernet jacks in public-facing areas (lobby, waiting rooms, service counters) are an easy entry point for attackers who plug in a laptop and start capturing traffic. Port security on your Cisco or Fortinet switches should limit each port to a single registered MAC address.
We’ve covered the broader threat landscape in our piece on defending VoIP networks against real-world attacks, and those lessons apply directly to agency environments.
Authentication and Monitoring
Enforce multi-factor authentication on every administrative interface. The web GUI on your PBX, the provisioning portal, the CDR (call detail record) dashboard. Default credentials on IP phones and VoIP gateways are published in vendor documentation that anyone can download. Change them during initial provisioning, and rotate admin passwords quarterly.
Warning: A common failure pattern in government IT: the agency contracts a systems integrator to deploy VoIP, the integrator configures everything with their own admin credentials, and then the contract ends without a proper handover. Your agency should own all administrative credentials from day one, documented in a secure password vault.
Log every administrative action and review those logs weekly. Look for login attempts from unfamiliar IP addresses, bulk changes to extension configurations, and after-hours access to call recording archives.
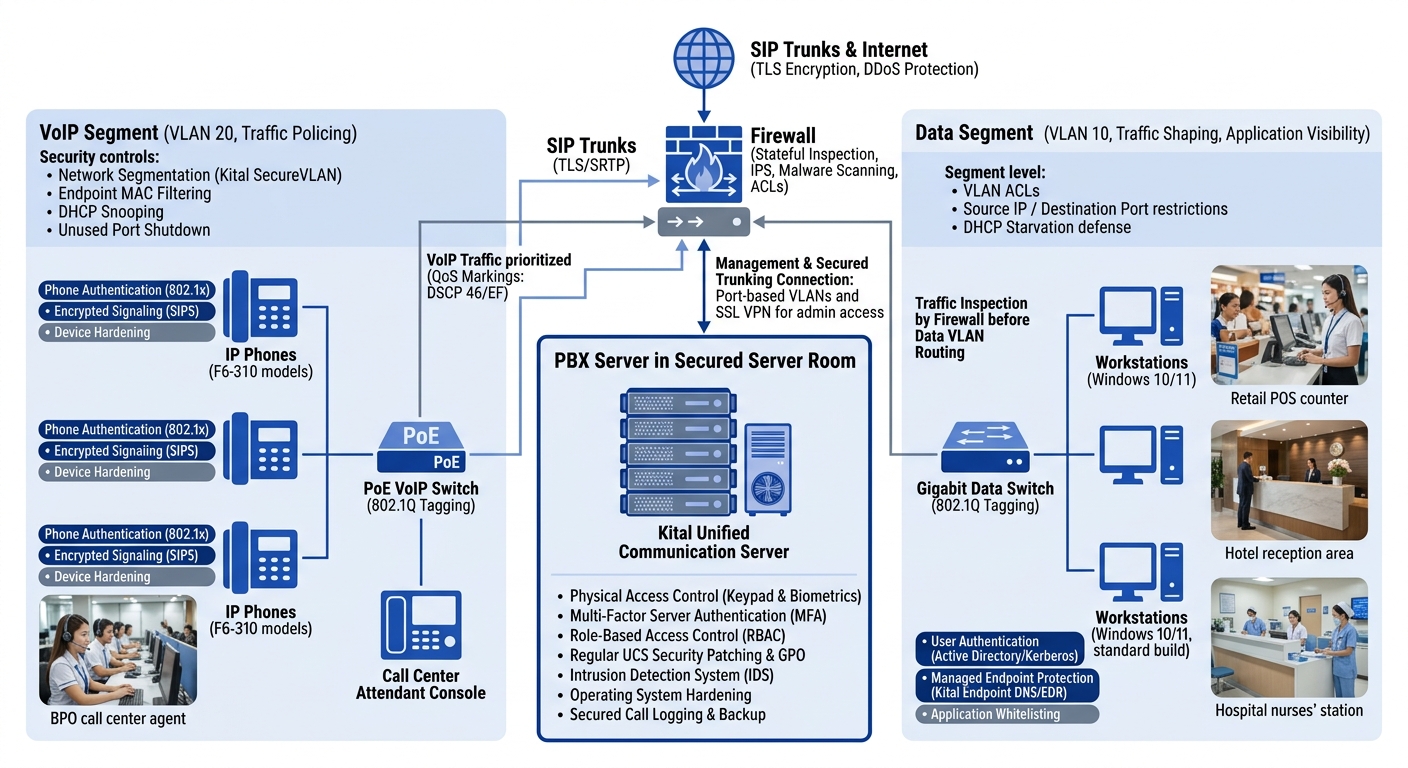
Network Planning and QoS Configuration
Voice is unforgiving of latency, jitter, and packet loss. A web page still loads if a few packets arrive late. A phone call turns into garbled noise. Network QoS for government VoIP requires deliberate design before the first handset is provisioned.
Bandwidth Assessment
Each concurrent VoIP call consumes between 30 Kbps (G.729 codec) and 90 Kbps (G.711 codec) of bandwidth, including protocol overhead. If your agency expects 50 simultaneous calls at peak hours, you need at minimum 1.5 Mbps of dedicated, QoS-prioritized bandwidth for voice alone. That figure doesn’t account for video calls or screen-sharing, which multiply bandwidth requirements by 5x to 20x.
Conduct a traffic analysis during the busiest two weeks of your fiscal quarter. Government offices in Metro Manila, Cebu, and Davao often hit peak call volumes during enrollment periods, filing deadlines, and disaster response events. Your bandwidth allocation should accommodate those spikes, not just average-day traffic.
For a detailed walkthrough, our guide on configuring QoS for VoIP on Philippine networks covers DSCP marking, traffic shaping, and queue scheduling step by step.
If your agency can’t show a current NTC Certificate of Registration during a spot audit, the entire phone system is operating illegally.
Prioritization and Traffic Shaping
DSCP value 46 (Expedited Forwarding) should be applied to all voice packets at the access switch. Every router and firewall in your network path needs a QoS policy that honors that marking. If even one hop along the path ignores DSCP tags, voice quality degrades unpredictably.
Don’t assume your ISP will honor your internal QoS markings once traffic leaves your WAN edge. Many Philippine ISPs reset DSCP values at their ingress point. If you’re running SIP trunks to a public carrier, ask the carrier explicitly whether they support end-to-end QoS, and get that commitment in writing in your service-level agreement.
Troubleshooting degraded call quality often leads back to network congestion issues that have nothing to do with the VoIP system itself. A single user running a large file transfer or a backup job during business hours can consume enough bandwidth to push voice packets into jitter territory.
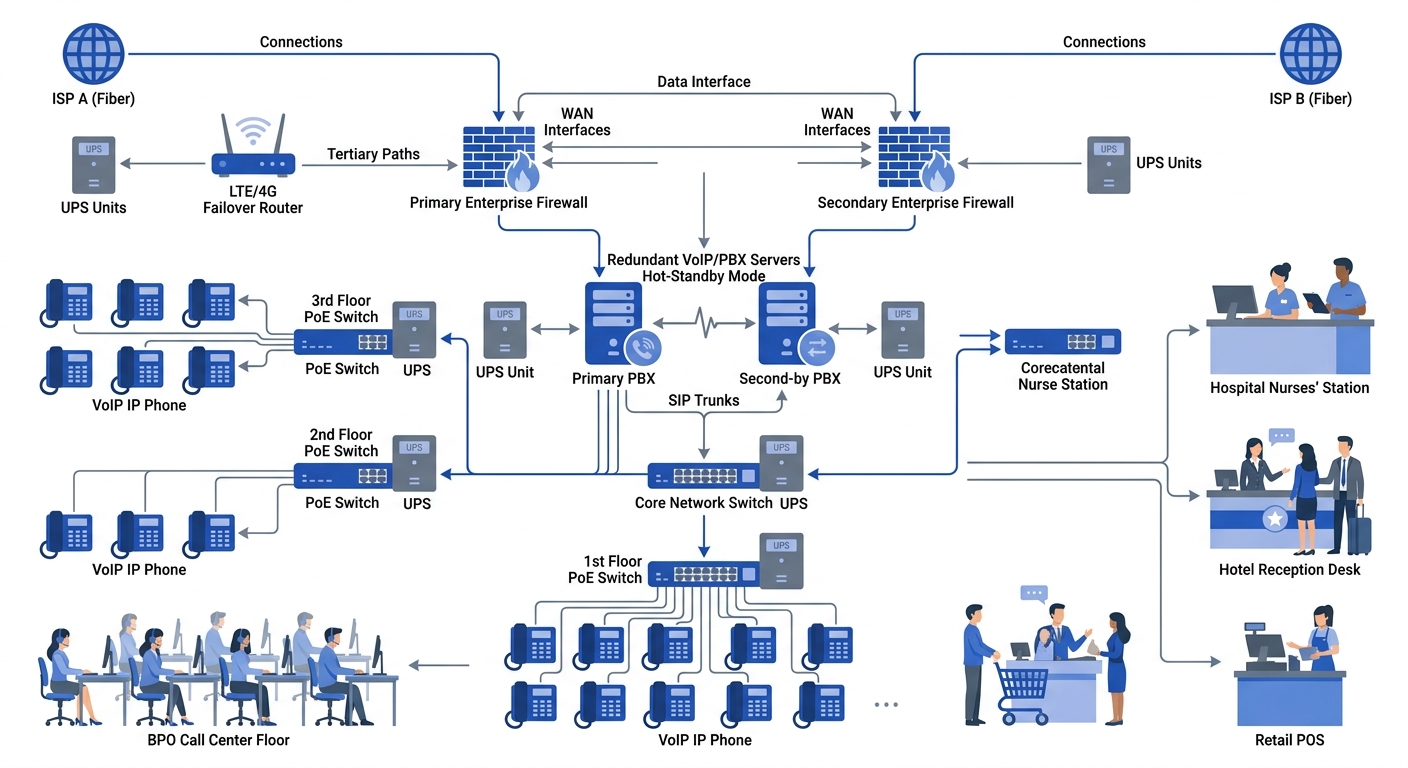
Redundancy and Failover
Government agencies cannot afford a total voice outage. Design for at least N+1 redundancy on your internet links. If your primary connection is PLDT fiber, your backup should be on a different carrier and a different physical path. An LTE failover link from Globe or Smart provides last-resort connectivity when both wired connections fail simultaneously.
Power redundancy matters equally. Every IP phone, switch, PoE injector, and PBX server in the voice path should be on an uninterruptible power supply. In provinces outside Metro Manila, where power interruptions are frequent, a generator with automatic transfer switch is a practical necessity, not a luxury.
Yeastar PBX systems support hot-standby configurations where a secondary unit takes over if the primary fails, and several Philippine government offices already run this setup for continuity during typhoon season. Pair that hardware redundancy with solid backup and recovery solutions so that configuration data, call recordings, and directory information survive a catastrophic failure.
Choosing Between On-Premises, Cloud, and Hybrid Deployments
The deployment model affects compliance, cost, and operational burden. On-premises VoIP gives your agency full control over data residency, which simplifies NPC compliance and eliminates concerns about call recordings stored on servers outside Philippine jurisdiction. The tradeoff is that your IT team owns all maintenance, patching, and security monitoring.
Cloud-hosted VoIP shifts that burden to a managed service provider. For smaller agencies or regional offices without dedicated IT staff, this can be the more practical path. But you need contractual guarantees that the provider stores data within the Philippines, holds relevant certifications (SOC 2 Type 2, ISO/IEC 27001), and will cooperate with NPC breach investigations.
Hybrid models work for agencies with a central office in Manila and satellite offices across the archipelago. The main site runs an on-premises PBX for maximum control, while remote offices connect through cloud-based extensions. If you’re weighing these options, our comparison of on-premises PBX advantages and drawbacks can help you map the right model to your agency’s resources.
Tip: Before committing to a deployment model, run a 30-day pilot with 5 to 10 users in one department. Test call quality during peak hours, verify that QoS policies hold under load, and confirm that your SIP trunks interoperate with the NTC-registered carrier. Pilots cost almost nothing compared to a full rollout that reveals problems at scale.
What Remains Unsettled
Philippine VoIP regulation hasn’t kept pace with how agencies actually use the technology. The NTC’s core circulars date to 2005, and while VoIP services are legal and recognized in the Philippines, the rules were written when SIP trunking was the primary use case. They don’t address WebRTC-based communications, Microsoft Teams Direct Routing, or AI-powered call routing systems that are now entering government contact centers.
The interconnection fee structure (PhP 1.00 for fixed, PhP 1.50 for mobile) also reflects a telecommunications landscape that has since evolved. Whether these fees will be revised, and how the NTC will classify newer communication platforms, are open questions that affect long-term procurement planning.
Agencies deploying VoIP today should build systems that meet current NTC and NPC requirements while keeping enough architectural flexibility to adapt when updated regulations arrive. That means choosing standards-based platforms, avoiding vendor lock-in where possible, and documenting your compliance posture thoroughly enough that auditors five years from now can trace every decision back to a policy rationale.