Cisco’s collaboration readiness assessment begins with a question most vendors skip entirely: how many separate communication platforms does your organization already run? The number matters because a UC platform doesn’t operate in a vacuum. It inherits your network’s security posture, your staff’s daily habits, and your compliance obligations the moment it goes live. The widespread assumption during unified communications selection is that comparing feature lists will surface the best fit. That assumption is wrong. The actual mechanism behind a successful UC deployment is a three-way alignment between what the platform demands from your security controls, what Philippine compliance standards require you to enforce, and how much operational change your people can absorb in a realistic timeframe.
When any one of those three layers is mismatched, the deployment either stalls in pilot or gets quietly abandoned within six months. Understanding how these layers interact gives you a far more reliable basis for UC platform evaluation than any spec sheet can.
The Security Model as a Boundary Condition
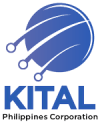
Every organization already has a security model, whether it was designed deliberately or just accumulated over years of IT decisions. That model includes how you authenticate users, how you segment your network, how you manage endpoints, and what your firewall rules actually permit.
A UC platform drops into whatever exists. If you’re running a flat network where SIP trunks, call managers, and video bridges all sit on the same Layer 2 segment, a cloud-first UCaaS product that assumes micro-segmented traffic will collide with your architecture on day one. The platform’s UC security requirements don’t adjust to match your reality. You either meet them or you don’t.
Practically, this means auditing three things before you look at any vendor shortlist:
- Authentication enforcement — Do you currently require multi-factor authentication for all users, or only for VPN access? UC platforms like Cisco Webex and Microsoft Teams assume MFA is already in place. If your organization uses single-factor passwords across the board, deploying these platforms securely means changing a fundamental user behavior first.
- Endpoint control — The University of California’s security controls guidance requires host-based firewalls and strong password or biometric locks on every device that touches sensitive systems. Philippine BPO call centers with BYOD policies face a gap here. If agents access UC tools from personal phones without mobile device management, the platform’s security assumptions break down.
- Network segmentation — Voice traffic, video conferencing, and messaging each have different bandwidth profiles and different risk profiles. We’ve covered why network segmentation is essential to enterprise UC security in depth before. The short version: if an attacker compromises one workstation on an unsegmented network, they get direct access to every UC component.
Your existing security model sets a hard boundary on which platforms you can deploy responsibly. A vendor might demo a beautiful interface, but if you can’t enforce the controls the platform assumes are in place, the demo is fiction.
How UC Security Requirements Map to Philippine Compliance
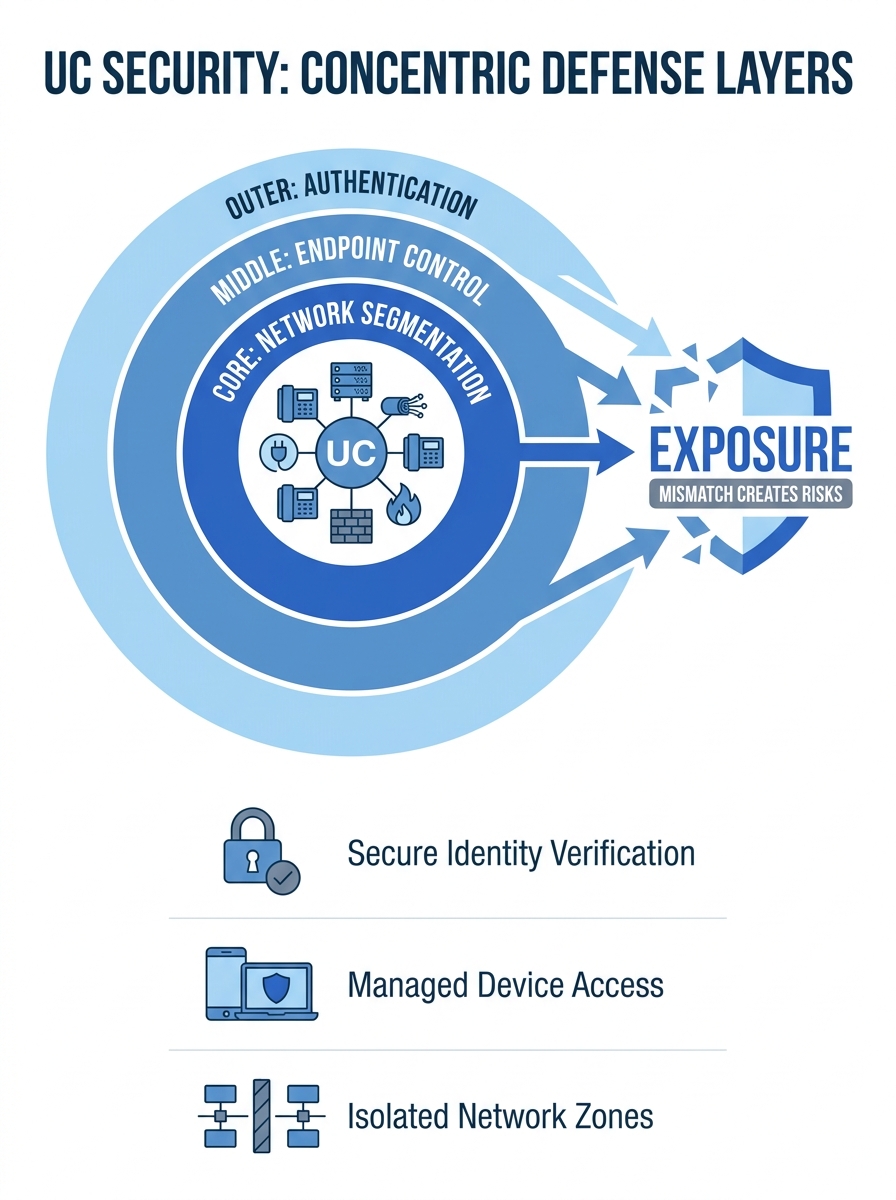
Philippine organizations operate under specific regulatory constraints that further narrow the field. The Data Privacy Act of 2012 (Republic Act 10173) requires adherence to three core principles when processing personal information: transparency, legitimate purpose, and proportionality. Any UC platform that handles customer data, call recordings, or messaging logs falls squarely within scope.
For a hospital in Cebu recording patient calls through a UC system, the compliance question isn’t “does this platform have call recording?” It’s “can this platform produce a detailed audit trail of who accessed those recordings, when, and from which device?” Thales Group’s analysis of the Philippine Data Privacy Act highlights that businesses need to be able to classify sensitive data wherever it lives and generate audit trails that prove compliance during NPC investigations.
Government agencies face additional layers. NTC registration requirements, DICT cybersecurity mandates, and procurement rules all shape which platforms are even eligible. Organizations evaluating communication systems for Philippine government agencies frequently discover that cloud-only UCaaS products can’t meet data residency preferences, while purely on-premise systems may lack the scalability for remote field offices in Mindanao or the Visayas.
Banks and financial services firms encounter yet another set of constraints. BSP circulars on information security and business continuity dictate how call data, transaction-related communications, and customer identity information must be stored and protected. For institutions exploring secure communications for Philippine banks, the UC platform evaluation must explicitly account for encryption standards, data retention policies, and disaster recovery requirements that go beyond what a general-purpose platform provides out of the box.
Warning: Philippine compliance standards don’t exist in isolation. A single UC deployment at a hospital, government agency, or bank may need to satisfy the Data Privacy Act, NTC regulations, and sector-specific rules simultaneously. Map all applicable mandates before you start comparing vendors.
The Unified Compliance Framework approach treats compliance mapping as a prerequisite, not an afterthought. It works by identifying common control requirements across multiple regulatory documents and flagging where a single security control can satisfy several mandates at once. For Philippine organizations juggling NPC, NTC, and industry-specific rules, this kind of mapping saves months of redundant work.
Change Capacity as a Sizing Constraint
Here’s where most UC projects actually fail. The security model checks out. The compliance mapping is done. Then the deployment stalls because the organization tried to absorb more change than it could handle.
Organizational change capacity is a measurable constraint, not a vague feeling. Ed Lawler and Chris Worley’s research on organizations “built for change” found that effective two-way communication systems are essential to building organizational capacity for change. The irony with UC deployments is obvious: you’re deploying a communication system, but the deployment itself demands communication skills that may not exist yet.
Consider a 200-seat BPO operation in Metro Manila migrating from a legacy PBX to a UCaaS platform. The technical migration might take two weeks. But the human migration involves retraining supervisors on new call monitoring tools, shifting agents from desk phones to softphones, changing how quality assurance teams pull recordings, and updating every client-facing SLA document. That human migration takes two to four months under realistic conditions.
Three factors determine how much change your organization can absorb:
- Current platform count — If your teams already juggle four or five separate communication tools (a PBX for voice, Zoom for video, Viber for internal chat, email for everything else), consolidating into one UC platform actually reduces complexity over time. But the transition period temporarily increases complexity. Organizations running fewer tools have less to consolidate but also less urgency to change.
- IT team depth — A five-person IT department supporting 500 users across three branches in Davao cannot simultaneously manage a UC migration, maintain the existing phone system during cutover, and handle the inevitable flood of support tickets from confused staff. Phased rollouts, department by department, become mandatory rather than optional. Our manufacturing migration playbook covers this staging approach in detail.
- Training infrastructure — Does your organization have a way to train 200 people on a new tool within a month? Some Philippine companies have dedicated L&D teams. Many don’t. Schools may have faculty who resist new platforms on principle. Hotels may have front-desk staff who rotate shifts and can’t attend a single scheduled training session. The training delivery mechanism shapes the rollout timeline as much as any technical factor.
The “best” UC platform is the one that matches your use cases, your security model, and your change capacity — not the one with the longest feature list.
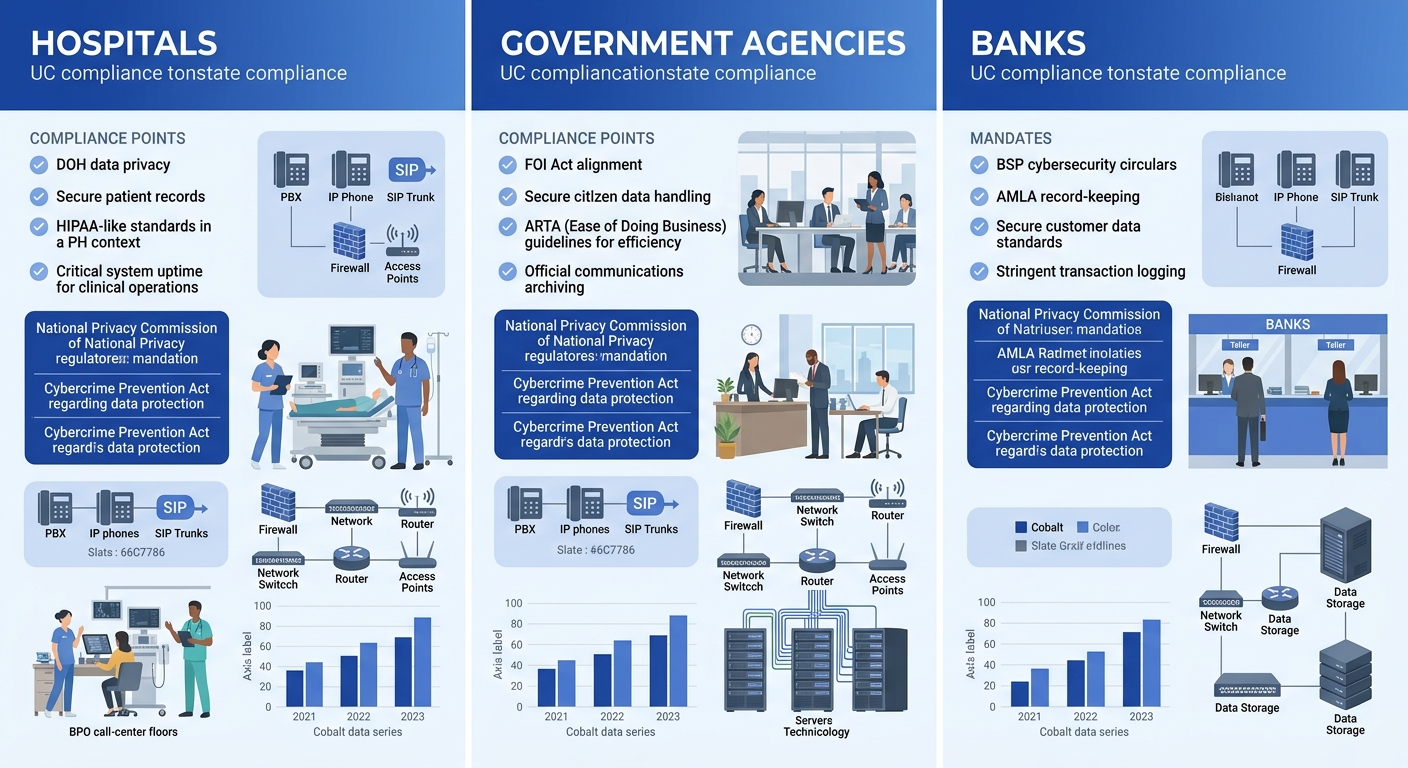
Running the Three-Way Fit
The mechanism works like this: you evaluate each candidate platform against all three layers simultaneously, and the platform that survives all three filters is your actual shortlist.
Layer one filter (security model): Does this platform’s minimum security requirements match what we can enforce today, or within 30 days with reasonable effort? If a platform requires micro-segmentation and you’re running a flat network, that’s a six-month infrastructure project before you even begin. Eliminate it or budget accordingly.
Layer two filter (compliance): Can this platform produce the audit trails, data classification, and access controls required by every regulation that applies to our sector? For organizations subject to both the Data Privacy Act and sector-specific rules, this filter often eliminates platforms that look great on paper but can’t generate the right reports during an NPC audit. Our government compliance and deployment checklist walks through the specific documentation requirements.
Layer three filter (change capacity): Given our IT team size, training infrastructure, and current number of communication tools, can we realistically deploy this platform within our target timeline? A 12-month rollout might be fine for a large government agency. A Makati-based fintech startup with 40 employees might need to be live in six weeks. The platform that requires the least behavioral change from end users scores highest here.
What’s left after all three filters is a very short list. Sometimes it’s one vendor. Sometimes it’s zero, which means you need to invest in one of the three layers before you can proceed.
Where the Model Breaks
This three-layer approach works well for organizations with stable operations and clear governance. It breaks down in predictable ways.
Mergers and acquisitions. When two Philippine companies merge, they bring two security models, two compliance postures, and two sets of user habits. The three-way fit has to be run twice, and the results rarely converge on the same platform. The pragmatic answer is usually to pick the platform that satisfies the stricter security model and design the training plan around the less tech-savvy workforce.
Rapid scaling. A BPO that wins a major offshore contract and needs to add 500 seats in 90 days doesn’t have time for a careful change capacity assessment. The urgency forces compromises. Security controls get configured after go-live rather than before. Compliance documentation happens retroactively. These shortcuts create debt that compounds.
Executive override. Sometimes the CEO’s golfing buddy sells Cisco, and the decision is already made before any evaluation happens. The three-layer model can still help here: run the fit analysis against the pre-selected platform and present the gaps honestly. At least the organization enters the deployment with eyes open about which risks it’s accepting.
Vendor lock-in from adjacent systems. If your organization already runs Microsoft 365 across every department, the gravitational pull toward Microsoft Teams is enormous regardless of what the security and change analysis says. The sunk cost in licensing, training, and integrations makes switching to a different UC platform genuinely expensive. The model accounts for this through the change capacity layer, but the financial reality can override even a clear technical mismatch.
The UC selection process that actually works in Philippine organizations treats feature comparison as the last step, not the first. Security model fit eliminates platforms you can’t protect. Compliance fit eliminates platforms you can’t audit. Change capacity fit eliminates platforms you can’t adopt within a reasonable window. What survives all three is the platform worth buying. If you’re working through this process and want help mapping it to your specific environment, reach out to discuss your requirements with a solutions consultant who understands the local regulatory and infrastructure landscape.