The Philippine government’s fixed broadband infrastructure ranks among the weakest in Southeast Asia for sustaining real-time voice traffic, and every VoIP deployment that ignores this reality fails in the same predictable way: the phones work during the pilot, call quality degrades within weeks of full rollout, and staff quietly revert to mobile phones and Viber group chats. The agency blames the VoIP vendor. The vendor blames the ISP. The actual culprit is a network layer that was never designed to carry voice in the first place.
This matters because the DICT’s push to digitize government services depends on reliable internal and citizen-facing communications. A city health office that can’t maintain a stable call with a rural health unit during a disease outbreak isn’t dealing with an inconvenience. It’s dealing with a systems failure that has direct public health consequences. The UNDRR’s own research on emergency telecommunications documents how natural hazards destroy telecom infrastructure and cause severe network disruptions, and the Philippines sits in the path of roughly twenty typhoons per year.
VoIP infrastructure design for government agencies can’t begin with choosing between Yeastar, Cisco, or a cloud-hosted platform. It has to begin with the network underneath.
Why Government Networks Break Voice Before Anything Else
Government agency networks in the Philippines were typically built for email, web browsing, and file transfers. These are all tolerant of latency spikes and packet loss. A 200-millisecond delay on loading a GSIS page is invisible to the user. A 200-millisecond delay on a voice call produces the kind of awkward conversational overlap that makes people hang up.
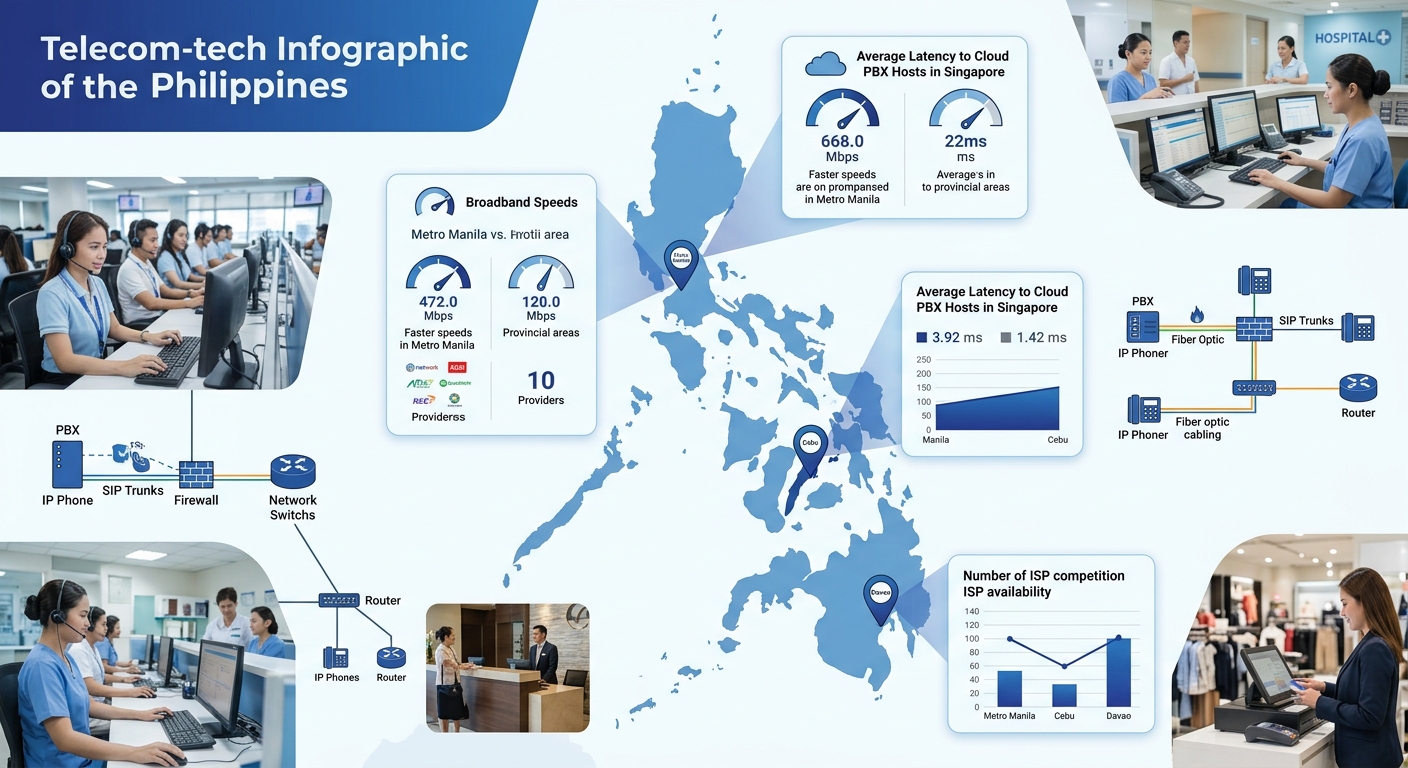
The World Bank has noted that the Philippines has been one of the slowest countries at promoting reforms for affordable broadband, with scores declining or only marginally improving across national broadband policy, competition, spectrum policy, infrastructure sharing, and universal access. That assessment directly affects government offices outside Metro Manila, where a provincial DENR field office might share a 10 Mbps DSL line across forty users, with no traffic prioritization and no redundant path.
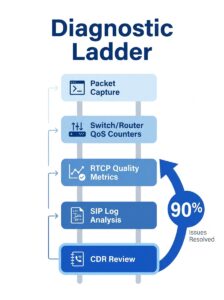
The typical failure sequence looks like this:
- The agency procures IP phones and a PBX (often on-premise, sometimes cloud-hosted).
- Phones are connected to existing network switches, sometimes on the same VLAN as workstations.
- Calls work well at low volume during testing.
- Once the full office is live, bandwidth contention during peak hours (9-11 AM, 1-3 PM) introduces jitter above 30 ms and packet loss above 1%, which is enough to make calls unintelligible.
- Staff stop using the desk phones. The procurement sits largely unused.
The equipment was fine. The configuration was probably fine. The network couldn’t support the traffic pattern.
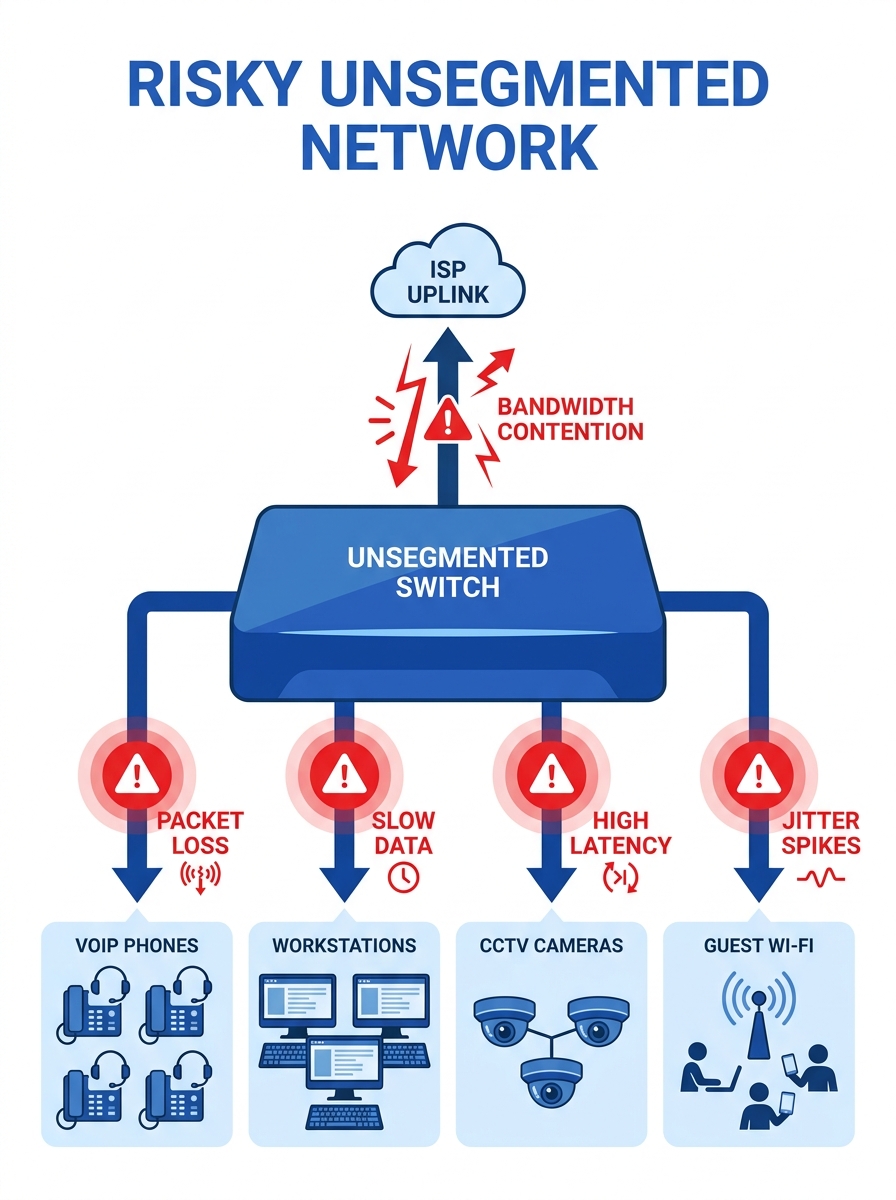
The Network-First Design Sequence
A network-first approach means you assess, fix, and validate the network before any VoIP hardware ships. The sequence matters because each step depends on the one before it.
Bandwidth Assessment with Realistic Margins
Calculate your concurrent call requirement and then double it. A 50-seat government office where ten people are on calls simultaneously needs roughly 1 Mbps of dedicated, prioritized bandwidth for voice alone (assuming G.711 codec at 87 Kbps per call including overhead). That sounds trivial until you realize the same pipe is carrying Windows updates, cloud backup jobs, video streams from security cameras, and the occasional YouTube session.
The key word is “dedicated.” You need either a physically separate internet circuit for voice or, more practically, a properly configured QoS policy that gives voice traffic absolute priority. If you’re unfamiliar with how to set this up on Philippine ISP connections, we’ve covered the specifics of configuring QoS for VoIP on local networks in detail.
VLAN Segmentation
Voice and data traffic must live on separate VLANs. This is non-negotiable for government deployments because it addresses both performance and security simultaneously. When a Fanvil or Yeastar IP phone connects to a network drop using a daisy-chain configuration (phone plugs into the wall jack, workstation plugs into the phone’s PC port), the switch must tag voice traffic on one VLAN and data traffic on another. Without this separation, a large file download on the workstation will directly compete with the voice stream on the same phone.
The segmentation requirement also aligns with government security expectations. As we’ve discussed in the context of why network segmentation is critical for unified communications security, keeping voice traffic isolated limits the attack surface and makes it harder for compromised workstations to intercept call data.
Switch and Cabling Audit
Many government offices run on switches that are a decade old, with Fast Ethernet (100 Mbps) ports and no VLAN or QoS support. These have to be replaced before VoIP goes live. Managed switches from vendors like Cisco Catalyst or even more budget-friendly options from Ruijie or HPE Aruba give you the per-port VLAN tagging and 802.1p priority marking that voice traffic requires.
Cabling is the other overlooked problem. Cat5 (not Cat5e, but the original Cat5) still exists in older government buildings, particularly in regional offices that haven’t been renovated since the 2000s. Cat5 can technically carry gigabit Ethernet over short runs, but signal degradation and crosstalk on aged cables with deteriorated terminations will introduce the kind of intermittent errors that wreck voice quality while leaving data applications seemingly unaffected. Budget for a cable certification sweep. It’s cheaper than troubleshooting phantom call-quality issues for months after deployment.
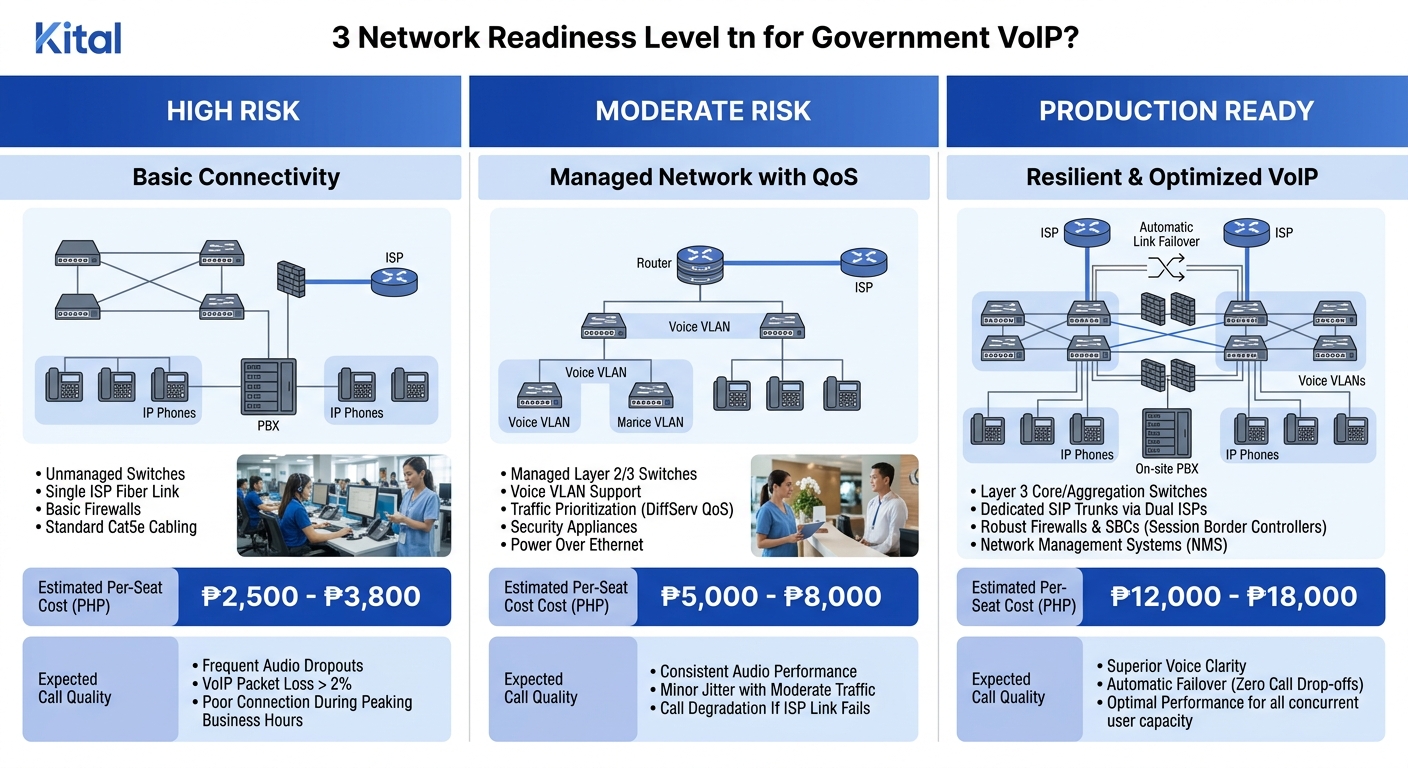
Designing Network Redundancy for Government-Grade Uptime
Government agencies have a specific operational requirement that private businesses can sometimes work around: they can’t close. A BIR district office can’t tell taxpayers to come back tomorrow because the phones are down. A PNP regional headquarters can’t miss incoming calls during a public safety event. This means network redundancy moves from “nice to have” to “required.”
The right question for a government VoIP deployment isn’t “which PBX should we buy?” It’s “what happens to our calls when the primary ISP goes down at 2 PM on a Monday?”
Cloud-hosted VoIP services inherently offer redundancy and failover solutions that keep communications running during network failures or natural disasters. But cloud-hosted failover only works if the agency’s internet connection to the cloud is itself redundant. A geo-redundant cloud PBX is useless when the single PLDT fiber line into a Quezon City government building gets cut by road construction.
Dual-ISP with Automatic Failover
The minimum viable redundancy setup for a government office running VoIP is two ISP connections from different providers, with different last-mile technologies if possible (one fiber, one fixed wireless, for example). A Fortinet FortiGate or even a mid-range Peplink router can handle automatic failover with session persistence, switching voice traffic to the backup link within seconds of detecting a primary link failure.
The ISP diversity matters. Two circuits from PLDT that both terminate at the same exchange are not true redundancy. If that exchange loses power or fiber, both links die together. Pairing PLDT fiber with a Converge or Globe fixed-wireless backup gives you genuinely independent failure domains.
On-Premise PBX as a Local Survival Node
For agencies in areas with particularly unreliable internet, an on-premise Yeastar P-Series PBX (or equivalent) can function as a local survival node. Internal extension-to-extension calls continue even when the internet is completely down. External calls fail over to a cellular trunk (using a GSM/4G gateway) as a last resort. This hybrid approach gives you the benefits of cloud management during normal operations while preserving basic calling capability during outages.
This is especially relevant for provincial and municipal offices outside the major metro areas. A DSWD field office in a third-class municipality in Samar has fundamentally different connectivity realities than one in Makati. The architecture has to account for both.
Philippine Broadband Challenges That Shape Every Design Decision
The policy environment in the Philippines creates constraints that VoIP architects in other countries don’t face. The World Bank’s analysis of Philippine broadband policy highlights that the country collects less in direct and indirect taxes from the telecom sector while the industry simultaneously calls for government support to address infrastructure challenges that prevent equitable connectivity delivery.
What this means practically for government VoIP deployments:
- Asymmetric bandwidth is common. Many ISP plans deliver far more download than upload capacity. VoIP needs symmetrical bandwidth because you’re sending and receiving audio simultaneously. A 50 Mbps download / 10 Mbps upload plan might look adequate on paper, but the upload constraint limits how many simultaneous outbound calls you can sustain at acceptable quality.
- Latency to international gateways varies wildly. If your cloud PBX is hosted in Singapore or Hong Kong, latency from a provincial office might be 80-120 ms on a good day and 200+ ms during congestion. On-premise or Manila-hosted PBX instances reduce this variable.
- Power stability is part of network design. A UPS on your PBX means nothing if the switch, router, and ONT (optical network terminal) aren’t also on battery backup. A complete voice-network power plan covers every device in the call path, typically requiring 30-60 minutes of runtime to bridge typical brownouts.
- Permits and right-of-way for fiber installation can take months. Secondary ISP circuit provisioning in government buildings often involves LGU permits, building administration approvals, and NTC coordination. Start this process at the beginning of the project, not after the PBX is already racked and waiting.
If you’re also working through the compliance and procurement side of a government VoIP project, the deployment checklist covering NTC compliance, security, and planning requirements addresses the regulatory specifics.
Failover Architecture Beyond the Internet Link
Network redundancy gets most of the attention, but a truly resilient VoIP infrastructure has failover thinking built into every layer.
Hardware Redundancy
The PBX itself can be a single point of failure. Yeastar’s hot standby feature (available on the P-Series) keeps a secondary unit synchronized and ready to take over if the primary fails. For Cisco deployments, Unified Communications Manager supports redundancy groups across multiple servers. The scale of the agency determines whether this level of hardware redundancy is justified, but for regional or national command centers, it should be standard.
Switches in the voice VLAN path should use redundant uplinks with link aggregation (LACP) or rapid spanning tree to handle individual link failures without dropping calls.
Endpoint Resilience
Desk phones from Fanvil or Yeastar can be configured with a primary and secondary SIP registration target. If the primary PBX becomes unreachable, the phone automatically registers with the backup. This registration failover typically completes in 30-90 seconds, during which the phone is offline. For agencies that need zero-gap failover, phones with dual-registration capability (registering to both targets simultaneously) close that window.
Trunk Redundancy
SIP trunks from Philippine telcos are the bridge between your internal VoIP system and the PSTN. A single SIP trunk from one provider is a single point of failure. Configuring two SIP trunk providers with automatic failover routing on the PBX ensures that if Globe’s SIP service goes down, calls automatically route through PLDT’s trunk (or vice versa). The per-minute cost difference between providers is negligible compared to the cost of a government office being unreachable for hours.
The Open Threads
Several questions remain genuinely unsettled for Philippine government VoIP deployments, and honest planning means acknowledging them rather than pretending they’re solved.
The DICT’s common tower policy and infrastructure-sharing frameworks are still evolving. Whether government agencies will eventually get access to dedicated backbone capacity, or continue competing for bandwidth on commercial ISP networks, will materially change the economics and architecture of every deployment discussed above.
NTC’s regulatory posture on VoIP numbering and emergency calling (E911 equivalent) for government agencies hasn’t been fully defined. Agencies deploying VoIP today are making reasonable assumptions about compliance requirements that may shift.
And the gap between Metro Manila connectivity and provincial connectivity isn’t shrinking fast enough. A network-first approach can compensate for weak infrastructure up to a point. It can’t fix a municipality where the best available connection is a 5 Mbps DSL line shared with the entire barangay hall. Until broadband reform catches up with the demand, government VoIP architects in those areas will keep designing around constraints rather than building on reliable foundations. The architecture patterns here give you the best odds of a system that stays running, but they don’t eliminate the underlying infrastructure gap that the country is still working to close.