Cisco Talos tracked the ten largest telephone-oriented scam campaigns between February 26 and March 31, 2026, and found that six of them ran entirely on disposable VoIP numbers. The phone numbers were provisioned through CPaaS providers, used for a few days, then abandoned before any reputation database could flag them. This finding punctures a widely held assumption in enterprise telephony security: that a phone number is a stable, traceable identifier. For scammers working the Philippine market and beyond, a VoIP number is now as disposable as a burner email address. The defenses most Philippine businesses rely on were designed for a world where that wasn’t true.
Understanding why these attacks succeed requires pulling apart the mechanism layer by layer, from how numbers get provisioned, to why VoIP reputation blocking can’t keep pace, to what detection alternatives actually exist.
How Disposable VoIP Numbers Get Provisioned at Scale
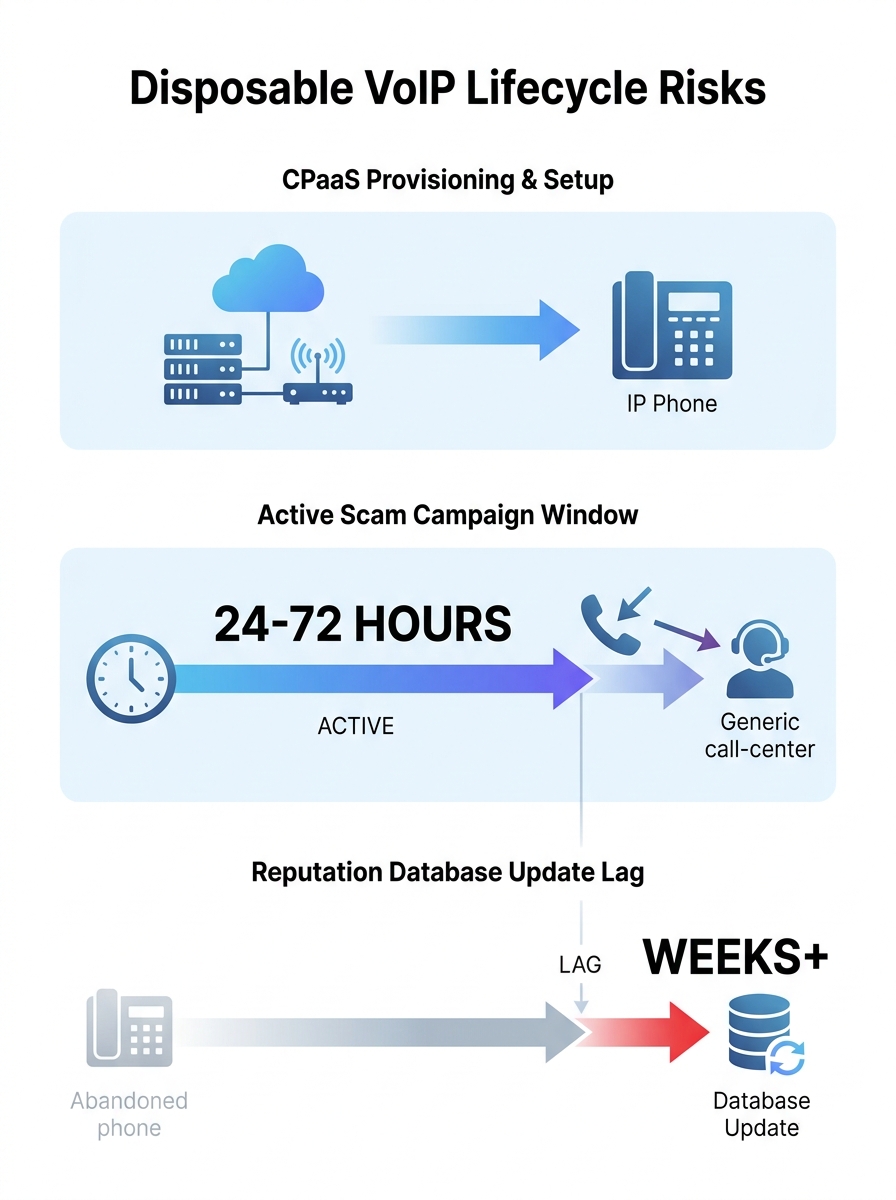
The raw material for these campaigns is cheap and abundant. Communications Platform-as-a-Service (CPaaS) providers sell API access that lets anyone provision phone numbers programmatically. A scammer with a script can acquire dozens of numbers in minutes, assign them to outbound campaigns, and release them within 48 to 72 hours. The cost per number ranges from a few cents to a couple of dollars per month, and many providers offer free trial tiers that require minimal identity verification.
Sinch was identified in the Cisco Talos research as the most frequently abused CPaaS platform in the observed campaigns, though the problem isn’t limited to any single provider. The business model of CPaaS platforms depends on frictionless provisioning. That same frictionless onboarding is what scammers exploit.
The numbers themselves look legitimate. They carry valid country codes, pass basic format checks, and ring through to real VoIP endpoints. When embedded in a phishing email or SMS, they’re indistinguishable from a legitimate business callback number. Attackers reuse VoIP phone numbers across multiple brand impersonation campaigns, switching between attachment formats like PDF and HEIC to evade email filters, while the phone number stays constant long enough to catch victims but short enough to dodge blocklists.
The Kill Chain: Telephone-Oriented Attack Delivery
The term for this attack pattern is TOAD (Telephone-Oriented Attack Delivery), and it represents a deliberate pivot away from clickable links. Instead of embedding a malicious URL in a phishing email, attackers embed a phone number. The email tells the target to call about an urgent invoice, a subscription renewal, or a suspicious charge. When the victim dials, they reach a live operator or an IVR system controlled by the attacker.
This is where the social engineering gets effective. A live voice conversation creates urgency and trust in ways that a phishing link cannot. The attacker walks the victim through installing remote access software, divulging credentials, or authorizing a payment. Because the victim initiated the call, their guard is lower. They chose to pick up the phone; nobody called them out of the blue.
For Philippine BPO operations and enterprises with large customer-facing teams, TOAD attacks are particularly dangerous. Employees trained to handle inbound and outbound calls all day may not flag a callback number in an email as suspicious, especially when it appears to originate from a local area code or a known vendor prefix. The mechanism exploits the very communication habits that make Philippine businesses operationally efficient.
Warning: TOAD attacks bypass email security entirely. Your spam filter may catch the email, but if it doesn’t, the attack payload is a phone call, which no email gateway inspects. Call spoofing detection has to happen at the telephony layer, not the inbox layer.
Why VoIP Reputation Blocking Can’t Keep Up
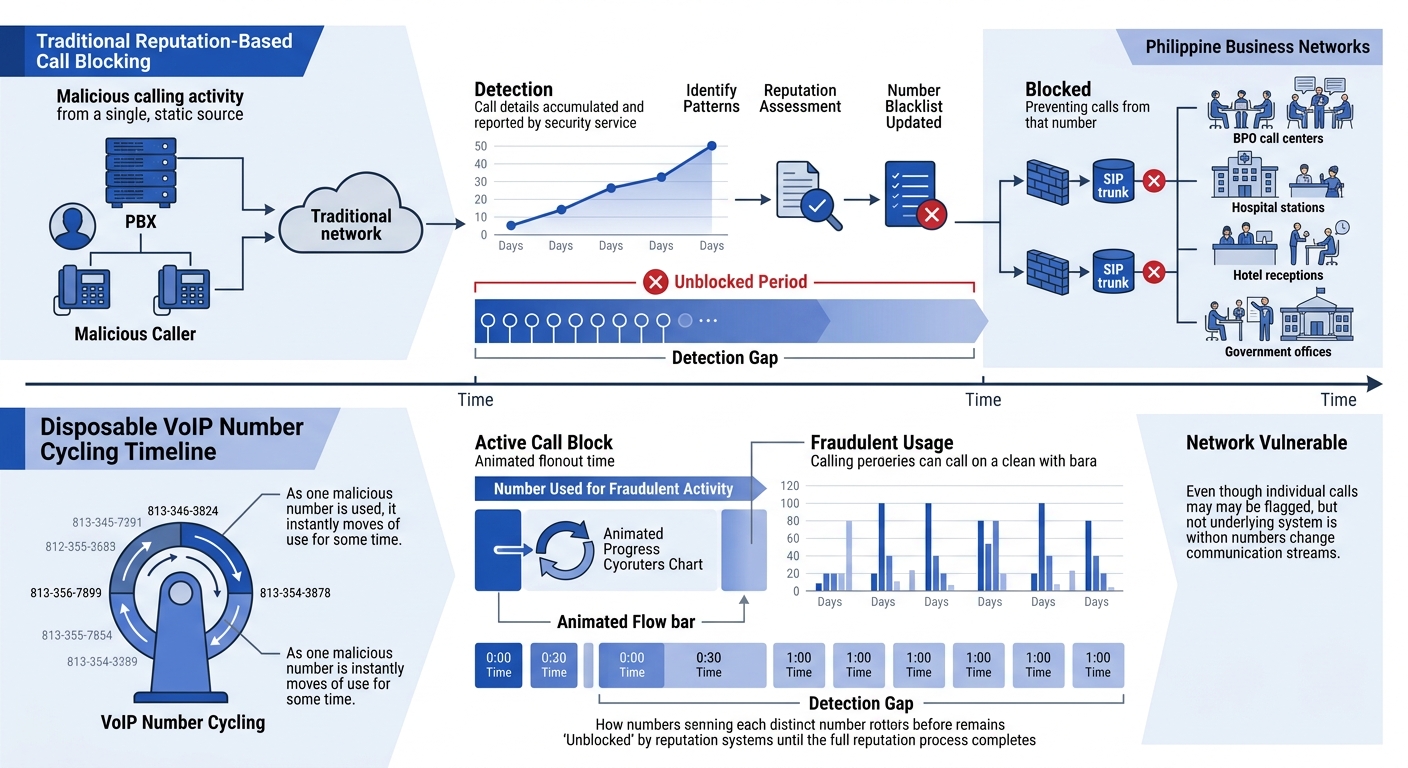
Traditional call-blocking services work on reputation scores. A phone number accumulates complaints, gets flagged by databases like Truecaller or carrier-level analytics, and eventually gets blocked or labeled as spam. This system works reasonably well against persistent spam operations that reuse the same numbers for weeks or months.
Disposable VoIP threats break this model through speed. The Cisco Talos data shows that attackers are burning through numbers faster than reputation databases update. A number might be active for two days, used across three or four campaigns targeting different brands, and then abandoned. By the time user complaints reach a threshold that triggers blocking, the number is already dead and a fresh one has taken its place.
The math is simple and unfavorable for defenders. If a reputation database updates every 24 to 48 hours, and an attacker cycles numbers every 24 to 72 hours, there’s a window where every number in the campaign is functionally clean. Multiply that by the ease of provisioning dozens of numbers simultaneously, and the attacker always has fresh inventory.
This is why organizations that depend solely on carrier-level spam filtering or third-party apps like Truecaller for enterprise telephony security are operating with a significant blind spot. Those tools catch the slow-moving threats. The fast-cycling disposable numbers sail through. If your enterprise has dealt with VoIP infrastructure security challenges before, this pattern adds a new dimension: the threat doesn’t come from someone breaking into your system, but from someone tricking your people through a system that appears to be working normally.
GSMA’s Disposable Number Check: API-Level Screening
The GSMA launched its Disposable Number Check service to address exactly this gap. Rather than waiting for reputation scores to accumulate, the service maintains a continuously updated database of over 200,000 unique disposable numbers sourced from more than 20 monitored websites where virtual numbers are sold or rented.
The mechanism is straightforward. When a user enters a phone number during account registration, OTP verification, or any identity-linked process, your application queries the GSMA API. The API checks whether that number matches a known disposable or virtual number pattern and returns a risk assessment. If the number is flagged, you can block it before sending an SMS OTP, preventing the disposable number from ever entering your system as a trusted contact point.
The GSMA has specifically highlighted the Philippine market as one where cross-sector action against scam infrastructure is urgent. Their recommendation includes standardizing threat-reporting practices and using telecom data insights with Open Gateway APIs for real-time fraud detection. For Philippine enterprises running customer-facing apps, e-commerce platforms, or patient portals, integrating disposable number checks at the sign-up stage is one of the few defenses that operates upstream of the attack rather than reacting after damage is done.
BeReal’s experience offers a concrete benchmark: after integrating an anti-fraud API that filtered out disposable phone numbers, the company reduced fake SMS traffic from 40% to 2%. That’s a dramatic compression of fraud surface, and it came from screening numbers at the point of entry rather than chasing them after the fact.
The attacker always has fresh inventory. If a reputation database updates every 24 to 48 hours and an attacker cycles numbers every 24 to 72 hours, every number in the campaign is functionally clean during its active window.
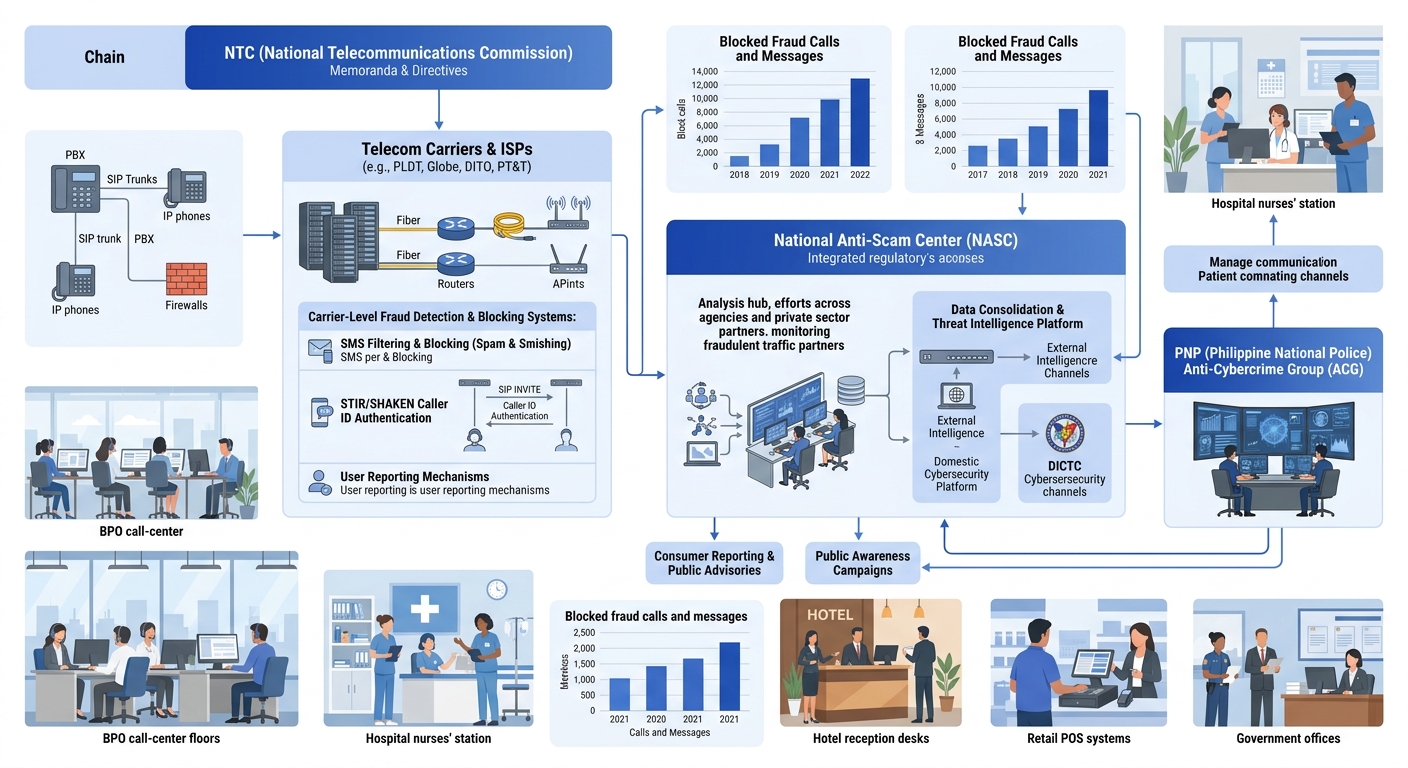
Philippine Regulatory Infrastructure Against Telephony Fraud
The Philippines has built a multi-layered regulatory response to telecom fraud over the past three years. Executive Order No. 208 established the Inter-Agency Committee on Anti-Illegal Telecommunications, which coordinates between the NTC, DICT, PNP Anti-Cybercrime Group, and the telcos themselves. The National Anti-Scam Center, launched in 2024, centralizes scam reports and aims to compress the time between a report and enforcement action.
The NTC’s current posture, as described in a recent Philippine Information Agency bulletin, promotes the B.I.R.D. framework: Block, Ignore, Report, and Delete suspicious messages. The NTC has also issued memoranda requiring telcos to implement AI-driven spam filters and comply with anti-spam directives that include blocking suspicious SMS and calls at the carrier level.
But here’s where the mechanism gets complicated for enterprise defenders. Philippine regulation primarily targets SMS-based scams and illegal SIM operations. The disposable VoIP number problem operates on a different plane. These numbers aren’t provisioned through Philippine telcos. They’re created through international CPaaS platforms, routed through global SIP infrastructure, and may never touch a Philippine carrier network until the final leg of the call. The NTC’s blocking mandates apply to numbers transiting Philippine networks, but the speed at which disposable numbers cycle makes proactive blocking at the carrier level a game of whack-a-mole.
The ongoing amendments to Republic Act No. 10175, the Cybercrime Prevention Act, are attempting to address emerging threats including deepfake calls and AI-generated voice attacks used in social engineering. These amendments matter because they expand the legal definition of what constitutes telecom fraud, which in turn affects what the NTC and law enforcement can act on. For Philippine businesses tracking data breach exposure, the connection is direct: the surge in leaked accounts reported in Q1 2026 creates a richer target list for TOAD campaigns, since attackers can personalize their phishing emails with real account details.
Enterprise-Grade Call Security Platforms
For organizations that need protection beyond carrier-level filtering and app-based blockers, dedicated voice security platforms exist. SecureLogix offers its ETM (Enterprise Telephony Management) system, a voice network security platform designed for both TDM and SIP environments. When deployed as part of their managed service, it applies policy-based controls to inbound and outbound calls, including authentication checks and anomaly detection.
TNS (Transaction Network Services) launched its Enterprise Voice Security suite specifically for inbound contact centers, combining call authentication with robocall mitigation. For Philippine BPOs handling calls on behalf of international clients, this type of platform-level security is increasingly a contractual requirement from enterprise customers who’ve been burned by TOAD attacks targeting their brand.
Mutare takes a data-driven approach to call spoofing detection, using accumulated intelligence about voice spam patterns to anticipate where attacks will shift next. As Rich Quattrocchi, their VP of Digital Transformation, describes it: they combine deep knowledge of enterprise voice systems with a large dataset that lets them stay ahead of bad actors while frameworks like STIR/SHAKEN continue to mature.
The practical integration question for Philippine enterprises is where these platforms sit in your existing architecture. If you’ve already built your VoIP infrastructure around Yeastar or Cisco Unified Communications, adding a voice security appliance means placing it inline on your SIP trunks, typically between your SBC (Session Border Controller) and your PBX. This is where solid network logging practices become essential. You need visibility into call detail records, SIP headers, and trunk utilization to tune the security platform without accidentally blocking legitimate traffic.
Tip: If your organization uses SIP trunking, ask your provider whether they perform any upstream filtering of known disposable VoIP ranges. Some carriers maintain internal blocklists that never surface to the customer. Knowing what your carrier already filters helps you avoid duplicating effort or, worse, assuming you’re protected when you’re not.
Where These Defenses Fall Short
Every layer of defense described above has a failure mode. The GSMA Disposable Number Check works at account registration and OTP verification, but it doesn’t help when someone receives a cold phishing email with a callback number they never need to register. Reputation-based blocking fails against fast-cycling numbers. Carrier-level filtering can’t touch numbers that originate outside Philippine networks. Enterprise voice security platforms add real protection but require capital expenditure and ongoing tuning that many mid-market Philippine businesses can’t justify for a threat they haven’t yet quantified.
The deepest structural problem is that phone numbers were never designed to be identity tokens. The global telephone numbering system was built for routing, not trust. Every defense mechanism layered on top is trying to retrofit authentication onto infrastructure that doesn’t natively support it. STIR/SHAKEN is the closest thing to a systemic fix, but adoption remains uneven globally, and Philippine carriers have not yet mandated it across all trunk types. Until they do, enterprises are left assembling patchwork defenses from carrier filters, API-level number screening, dedicated voice firewalls, and employee training.
The most resilient stance for a Philippine enterprise right now is to treat phone numbers the way security teams already treat URLs and file hashes: as indicators that require real-time validation, not as trusted identifiers. That means clustering analysis on inbound numbers, cross-referencing against known disposable ranges, and training frontline staff to treat callback numbers in emails with the same suspicion they’d apply to an unfamiliar link. If your network segmentation already isolates voice traffic from data traffic, you have a foundation for applying call-level security policies without disrupting broader network operations. If it doesn’t, that’s the place to start, because bolting voice security onto a flat network creates exactly the kind of gaps these attacks are designed to find.