Philippine chief executives rank among the world’s most aggressive AI adopters, according to an IBM study published May 12, with the majority already relying on AI-generated insights for strategic decisions. That confidence sits on top of a $42 billion BPO industry employing 1.97 million specialists, per an Inquirer analysis from May 6. And yet the unified communications architecture underneath most of these enterprises still looks like it was designed for 2019: flat networks, siloed voice systems, and QoS policies bolted on after the fact.
The gap between executive ambition and infrastructure reality is where this year’s enterprise UC transformation will either succeed or quietly collapse under its own weight.
The Conference Season That Rewrote the Playbook
March and May of 2026 produced a concentrated wave of vendor announcements that collectively redefined what “unified communications” means for enterprise buyers.
At Enterprise Connect 2026 in March, RingCentral launched AIR Pro, Zoom unveiled AI Companion 3.0, and Dialpad rolled out agentic AI upgrades. All were production-ready platforms designed to automate workflows and enhance customer engagement. Salesforce introduced Agentforce Contact Center, merging AI, CRM, and voice into a native CCaaS offering. Mitel, historically an on-premise stronghold, made its own AI play.
Then in May, Extreme Networks used its Extreme Connect 2026 conference to unveil Agent ONE, a second-generation AI layer built on Platform ONE that spans Wi-Fi 7 access points, fabric-ready switching, and network-level intelligence. Twilio followed at SIGNAL 2026 by unifying voice, email, and messaging under a single SDK and billing commitment.
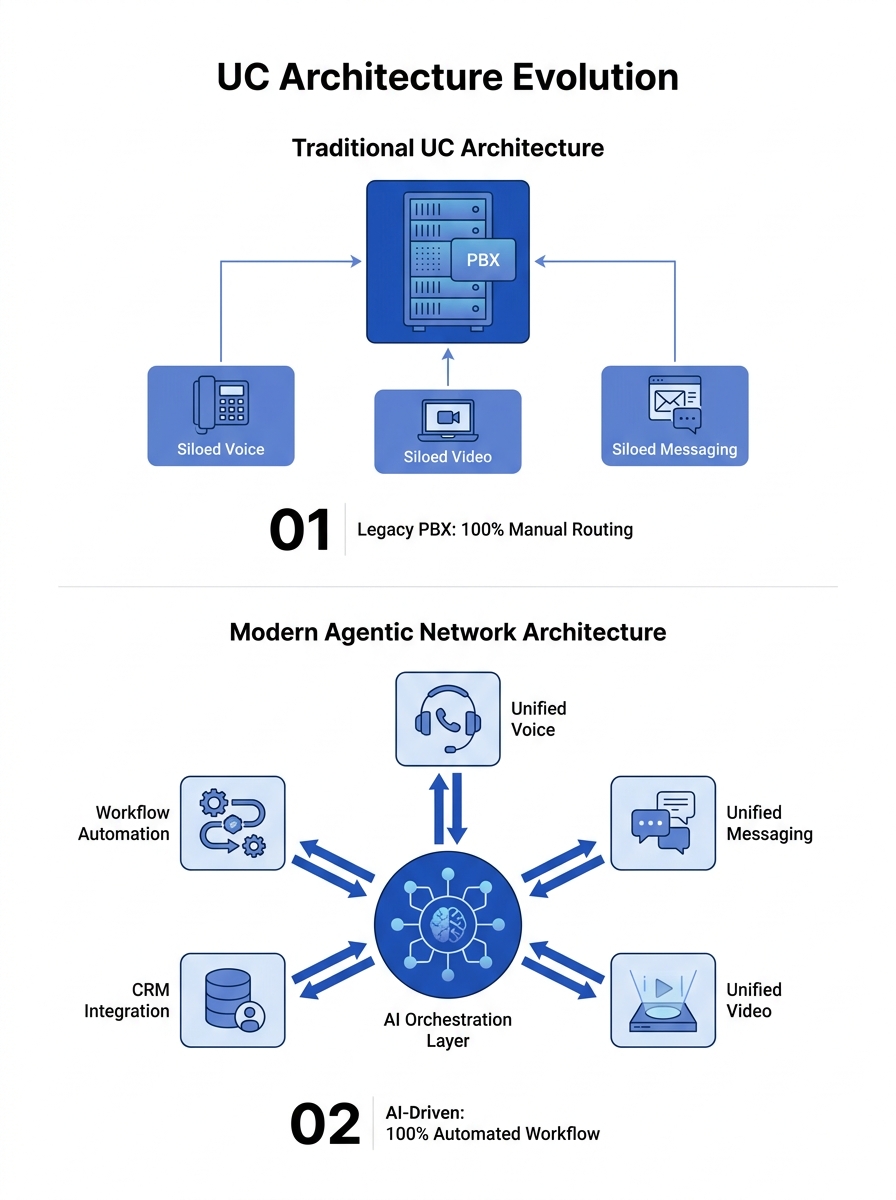
The shared thesis across all of these announcements: communication infrastructure should function as a communication operating layer, an intelligent substrate that routes, prioritizes, and even initiates interactions based on context rather than waiting passively for human commands.
What “Agentic Networks” Actually Means in Practice
The term agentic networks has been circulating since late 2025, but it landed with specificity at this year’s conferences. The concept describes the shift of communication from a back-office utility into a strategic layer that drives operational efficiency and AI-human collaboration.
In concrete terms, an agentic network is a unified communications architecture where AI agents can:
- Initiate outbound communications based on CRM triggers (a support ticket escalation automatically calls the customer)
- Route interactions across channels based on real-time context rather than static IVR trees
- Monitor call quality, presence data, and network health simultaneously, then adjust routing before a problem becomes audible
- Generate post-interaction summaries, action items, and follow-up tasks without human prompting
This is different from the “AI features bolted onto existing platforms” approach that UC Today describes as a common misunderstanding of AI-native UCaaS. The real architectural shift runs deeper: AI is embedded into the platform itself, analyzing data across voice, presence, and messaging in unified context.
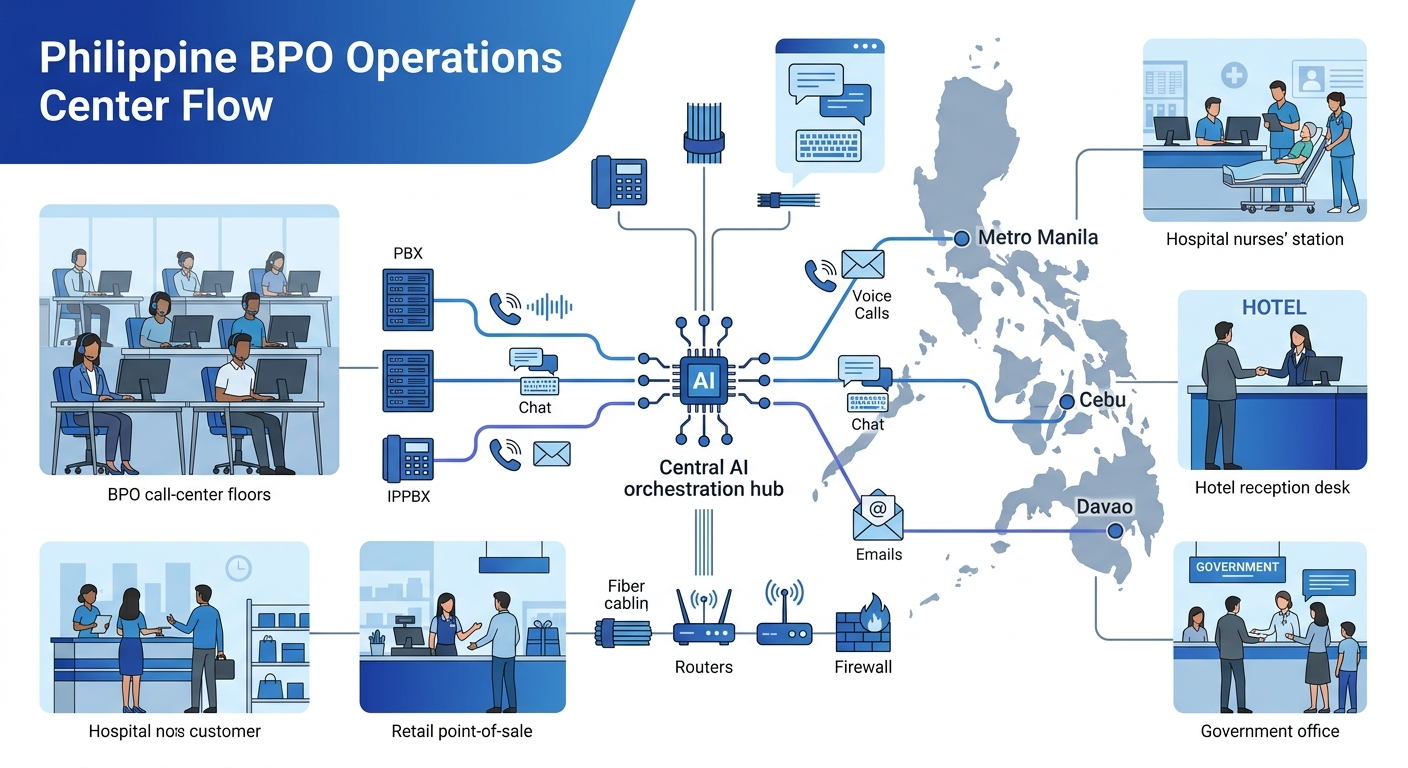
For Philippine BPO operations handling tens of thousands of concurrent interactions across Metro Manila, Cebu, and Davao, this distinction matters enormously. A 200-seat call center adding a chatbot to its existing Asterisk PBX is doing something very different from a 2,000-seat operation where AI agents handle tier-one inquiries end-to-end while routing complex cases to human specialists with full conversation context already attached.
The Security Problem Nobody at These Conferences Solved
Here’s where the executive enthusiasm from that IBM study runs headlong into physics. Agentic AI expands enterprise attack surfaces through broad permissions and unreviewed deployments, increasing lateral movement risks, according to a Hacker News analysis published this week.
Think about what an AI agent needs to do its job on an agentic network: access to your CRM, your call recordings, your presence data, your customer database, and your network routing tables. If that agent sits on a flat network with no segmentation, a single compromised endpoint could expose everything the agent touches.
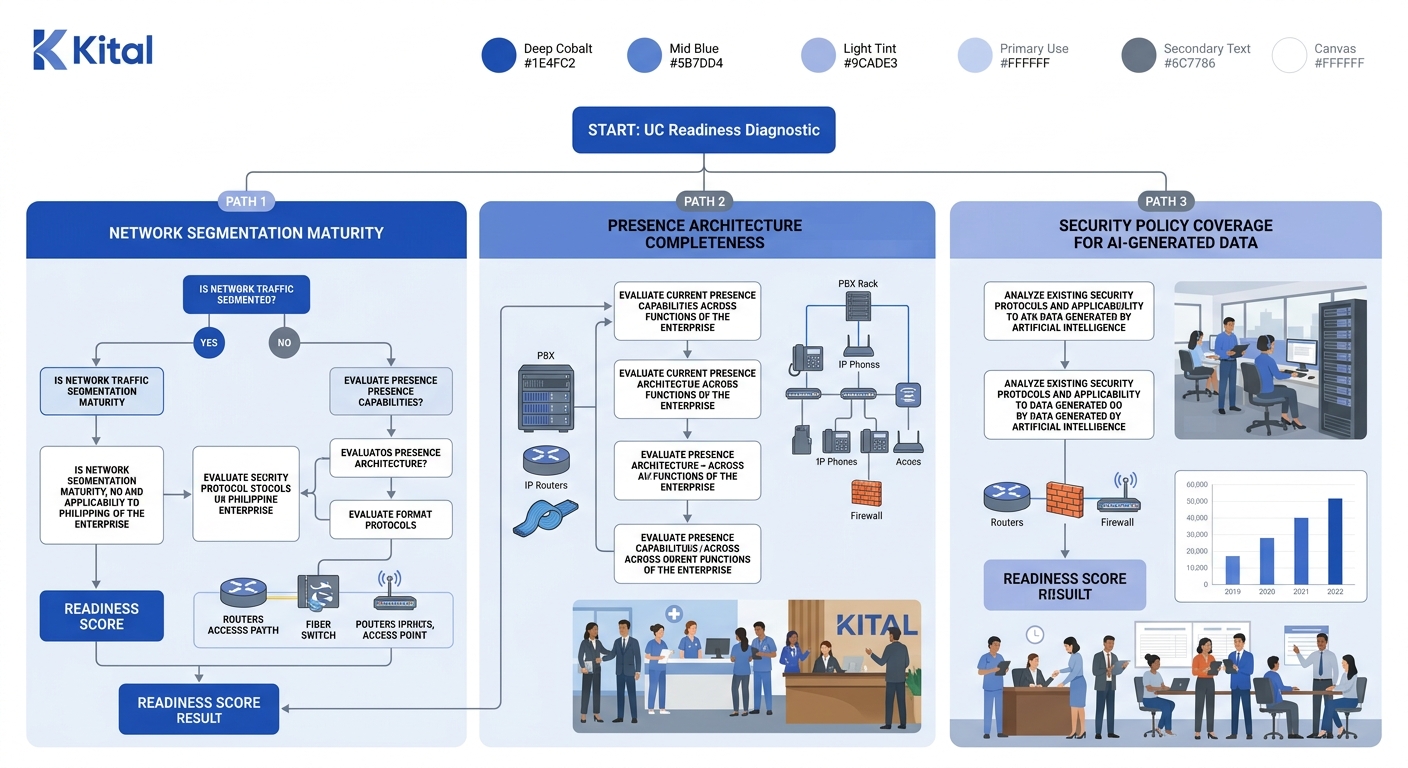
The data here is uncomfortable. Only one-third of organizations globally have fully implemented both macro-segmentation (VLANs) and micro-segmentation (tools like Cisco TrustSec or Fortinet FortiNAC). That leaves the majority of enterprises exposed to the exact lateral movement that agentic AI amplifies. We’ve written before about why network segmentation is prerequisite to any serious UC strategy, and the argument gets stronger with every AI agent added to the network.
Warning: Deploying agentic AI on a flat, unsegmented network means every AI agent becomes a potential pivot point for attackers. VLANs alone aren’t sufficient. You need strict inter-VLAN firewall rules (default-deny on everything except required ports like SIP 5060/5061 and SRTP) plus micro-segmentation at the workload level.
For Philippine enterprises specifically, the risk compounds across multi-site deployments. A BPO with agent VLANs in Cebu that can reach the entire data center in Manila has no meaningful segmentation at all. The Philippines recorded 624,400 leaked accounts in Q1 2026, a 76.8% surge in data breaches, and that threat environment is escalating at the same time enterprises are widening their attack surface with AI.
Only one-third of organizations globally have fully implemented both macro- and micro-segmentation, and every AI agent you add to an unsegmented network multiplies the blast radius of a single breach.
PLDT’s Agentic AI Bet and What It Signals
PLDT’s deployment of KAI, an agentic AI conversational platform built on UiPath’s architecture, made it the first ASEAN telco using agentic AI in production for enterprise client engagement. The deployment went live the week of April 24 and integrates AI directly into UC workflows for PLDT’s enterprise sales and support teams.
What makes this significant beyond the press release: PLDT is simultaneously the country’s largest telecom provider and one of its biggest enterprise customers. If PLDT’s own internal deployment requires the kind of segmented, AI-aware network architecture the industry is describing, that sets the benchmark for every other Philippine enterprise considering the same path.
The company’s parallel investments tell a consistent story. Its push toward cloud-first infrastructure, rural broadband expansion, and optical wireless connectivity all point toward a carrier building infrastructure with AI workloads in mind, from the physical layer up. Microsoft and Cisco are expected to push their own “agentic co-worker” visions at InfoComm 2026 on June 18, but questions remain about hardware compatibility and actual ship dates for on-premise AI execution.
Where Philippine Enterprises Actually Stand
The Philippine government’s digital agenda creates a top-down push toward modernized ICT infrastructure: the eGov PH Super App, the Cloud First Policy, and the National Broadband Plan all assume enterprises will be running modern, API-driven communication stacks. Manufacturing is moving toward process automation and predictive maintenance. BPOs face pressure from agentic AI competition. Hospitals and schools are adopting hybrid communication models.
But the infrastructure underneath these ambitions varies wildly. A Manila-based fintech with a Yeastar P-Series Cloud Edition and Fortinet-segmented network is architecturally ready for AI-native platforms. A provincial hospital running an aging Panasonic PBX on a flat network with no QoS is not. The gap between these two scenarios represents the real enterprise UC transformation challenge.
Three specific bottlenecks keep appearing across deployments:
Presence architecture gaps. AI agents need accurate presence data to route intelligently: who’s available, on which channel, at what capacity. Most Philippine UC deployments treat presence as an afterthought rather than a foundational layer, which means AI agents make routing decisions on stale or incomplete information. An agentic network that can’t see who’s actually available is just an expensive auto-attendant.
The VoIP-to-UC maturity gap. Many organizations think they have unified communications because they have IP phones. They don’t. If your voice system, video conferencing, and messaging exist as three separate platforms with no shared presence, routing, or analytics layer, you’re running IP telephony, not a unified communications stack. Agentic networks require the full UC layer to function.
Security posture that can’t keep pace. Each AI agent that touches customer data needs its own access controls, audit trails, and data retention policies. AI generates volumes of transcripts, summaries, and action items that fall under the Data Privacy Act. Most enterprises haven’t extended their security models to cover these AI-generated artifacts, and the NTC’s compliance framework hasn’t caught up either.
The Vendor Landscape Is Consolidating Fast
Twilio’s SIGNAL 2026 announcement (one platform, one SDK, unified billing) is the latest signal that the vendor landscape is compressing. RingCentral’s AIR Pro, Zoom’s AI Companion 3.0, and Salesforce’s Agentforce Contact Center all point in the same direction: vendors want to own the entire communication operating layer, from network to AI to analytics.
For Philippine enterprises evaluating platforms, this consolidation creates a timing problem. Committing to a vendor’s agentic AI stack today means betting on their ability to deliver on roadmap promises over the next 18 to 24 months. And if you’re running a hybrid deployment (say, a Yeastar PBX on-premise with RingCentral cloud services), you need to evaluate whether your vendor’s agentic AI layer works across both environments or only in their cloud. Most don’t support hybrid well yet.
The practical question for a 500-seat BPO weighing infrastructure investment against budget constraints: do you wait for vendor consolidation to settle, or start building the segmented, presence-aware network foundation that any future agentic platform will require? The infrastructure work is vendor-neutral. The AI layer isn’t.
What These Numbers Still Can’t Answer
The $42 billion BPO revenue figure, the IBM study’s executive confidence scores, and the one-third segmentation stat all paint a picture of an industry accelerating toward AI-native platforms while the infrastructure beneath it lags behind. But several critical data points remain missing.
Nobody has published reliable numbers on how many Philippine enterprises have actually deployed agentic AI in production UC environments versus pilot or proof-of-concept stages. The vendor announcements from Enterprise Connect and Extreme Connect are impressive, but conference demos don’t equal production workloads running at scale in a Makati office tower or a Cebu IT park.
We also lack good data on the cost differential between retrofitting an existing UC deployment for agentic capabilities versus building from scratch. For the IT director at a mid-sized BPO, that number matters more than any conference keynote.
And the security question remains largely theoretical until real-world incident data emerges from enterprises running agentic AI on their UC platforms. The attack surface expansion that analysts warn about is logical and well-argued, but we won’t know the actual risk magnitude until these deployments have been in production long enough for threat actors to target them.
What we do know: the architectural direction is set. Philippine enterprises that treat agentic networks as a future concern rather than a present infrastructure requirement will find themselves retrofitting under pressure. Retrofitting a flat network for AI workloads costs more, takes longer, and disrupts operations far more severely than building segmentation and presence architecture in from the start. The next quarter’s deployment data from PLDT’s KAI rollout and the first wave of BPO agentic AI implementations will tell us whether the industry’s confidence is well-placed or running ahead of its own infrastructure.