SIP was ratified as an IETF standard in 1999 with no built-in encryption, no mandatory authentication, and no integrity checking on signaling messages. That single design decision, which prioritized interoperability and rapid adoption over security, created an attack surface that researchers have since mapped across three distinct layers: network, transport, and application. For Philippine enterprises running voice traffic over shared IP infrastructure, every one of those layers is now actively targeted.
Understanding how we arrived at the current threat landscape matters because the defenses available today didn’t emerge all at once. They were built in response to specific attack techniques, each generation plugging gaps the previous one left open. Here’s how that chronology unfolded, and what it means for the architecture you should be building right now.
When SIP Shipped Without Armor
The Session Initiation Protocol was designed to be lightweight. It borrowed heavily from HTTP’s request-response model, used plaintext headers, and transmitted call setup information in the clear. At the time, voice traffic still ran primarily over dedicated TDM circuits, so security through network separation was the default assumption. IP telephony was a research curiosity, not production infrastructure.
That assumption collapsed fast. As enterprises migrated to SIP-based call signaling in the mid-2000s, voice traffic suddenly shared the same Ethernet segments, switches, and routers as email, web browsing, and file transfers. A compromised workstation on the data VLAN could now capture SIP INVITE packets, reconstruct call metadata, and even intercept RTP media streams carrying the actual audio.
The SIP specification included optional security extensions like Digest Authentication and S/MIME for message encryption, but adoption was spotty. PBX vendors shipped products with these features disabled by default because enabling them introduced compatibility issues between endpoints from different manufacturers. Philippine enterprises deploying their first IP-PBX systems during this period inherited all of these weaknesses.
Two Attack Classes That Define the Threat
By the late 2000s, security researchers had categorized SIP-based attacks into two broad families. A study combining rule matching and state transition models identified these as malformed SIP message attacks and SIP flooding attacks, and that taxonomy still holds.
Malformed SIP messages exploit parsing vulnerabilities in PBX software and endpoint firmware. An attacker sends a SIP INVITE or REGISTER packet with intentionally broken headers: oversized fields, unexpected characters, missing required parameters. If the receiving system doesn’t validate input correctly, it crashes, enters an undefined state, or leaks memory. The IETF’s own SIP Torture Test Messages (RFC 4475) document exists precisely because developers need standardized test cases for this type of input. But as one analysis of SIP security tools noted, the public availability of those test cases also gives attackers a roadmap for what parsers might handle poorly.
SIP flooding attacks are the VoIP equivalent of volumetric DDoS. The attacker sends thousands of REGISTER or INVITE requests per second, exhausting the PBX’s ability to process legitimate calls. Research into deep analysis intruder tracing for flood attacks describes these as “the most difficult threats for end-point servers” to handle, because the traffic looks structurally similar to legitimate SIP traffic. A BPO call center in Makati handling 200 concurrent calls generates a high volume of SIP transactions under normal operation, making it harder to distinguish an attack from a busy Monday morning.

These two categories branch into specific techniques: toll fraud through registration hijacking, eavesdropping via RTP interception, caller ID spoofing through header manipulation, and denial of service through resource exhaustion. The surge in telephony-based scam campaigns using disposable VoIP numbers has made several of these techniques commercially profitable, which means the volume of attacks keeps climbing.
Network Segmentation Becomes the First Real Defense
The earliest effective countermeasure didn’t require new hardware or software. It required rethinking how the network was structured.
Voice VLAN segmentation isolates SIP signaling and RTP media onto dedicated Layer 2 broadcast domains, separate from general data traffic. An attacker who compromises a laptop on the data VLAN can’t directly reach the voice VLAN without bypassing inter-VLAN routing policies. This separation also makes VoIP packet analysis considerably easier, because traffic captures on the voice VLAN contain only voice-related protocols rather than the noise of web browsing and file downloads.
For Philippine enterprises, implementing voice VLANs requires switches that support 802.1Q tagging and LLDP-MED (or CDP for Cisco shops) so that IP phones automatically negotiate their way onto the correct VLAN. We’ve written extensively about why network segmentation is a prerequisite for any unified communications deployment, and the security argument reinforces the performance one: segmentation protects voice quality and reduces the blast radius of attacks simultaneously.
But segmentation alone has limits. It stops lateral movement from compromised data endpoints, yet it does nothing about attacks originating from the internet and targeting your PBX’s public-facing SIP trunk. That gap drove the development of the next layer in the defense stack.
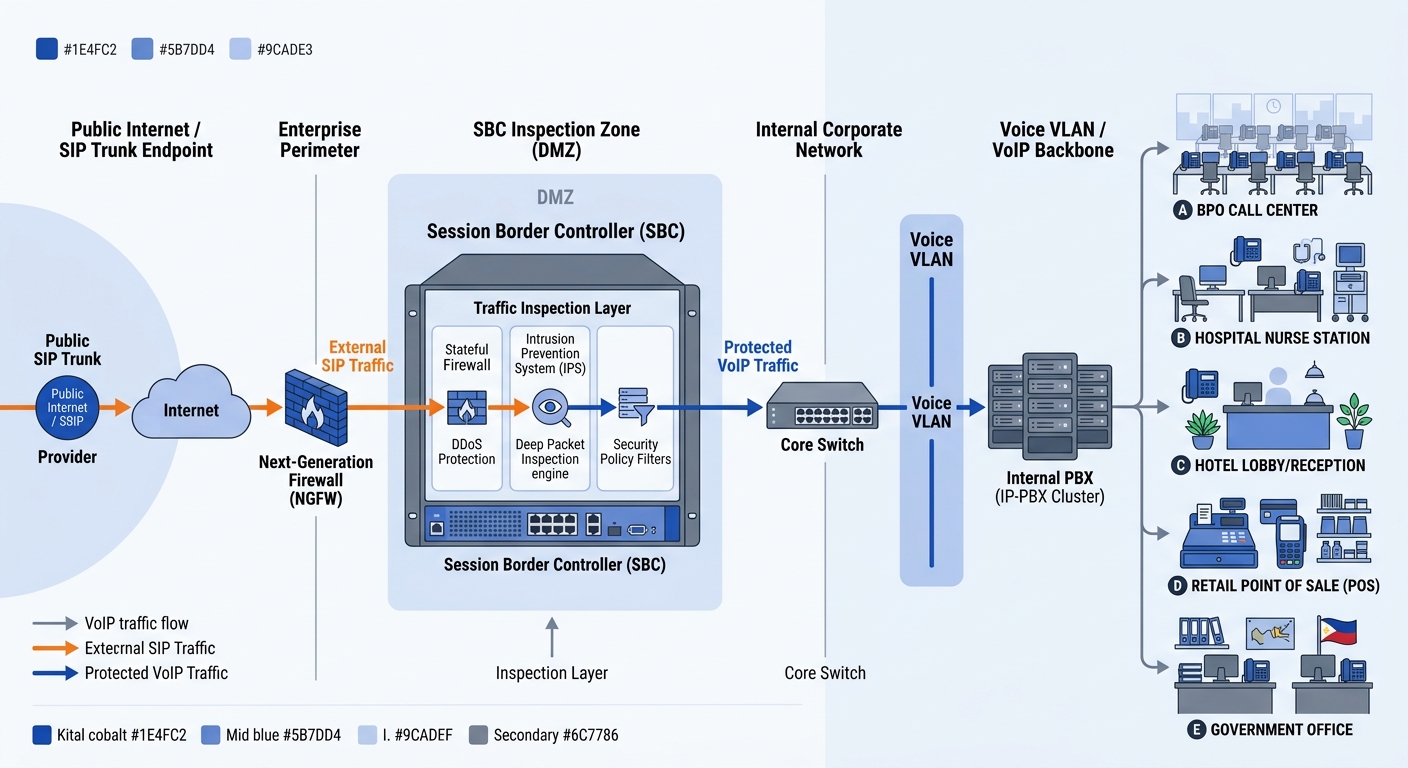
Session Border Controllers Enter the Picture
Session Border Controllers (SBCs) emerged as purpose-built security appliances for voice traffic. Unlike general-purpose firewalls, SBCs understand SIP at the application layer. They can inspect INVITE headers, enforce rate limits on REGISTER requests, normalize malformed messages before they reach the PBX, and topology-hide your internal network addressing from external callers.
As Verizon’s documentation on VoIP attacks describes, an SBC “acts as a first line of defense against service theft, spoofing, and DDoS” targeting voice infrastructure. For a Philippine hospital or government agency running SIP trunks to PLDT or Globe, the SBC sits between the public SIP trunk and the internal PBX, inspecting every inbound session before it touches your call processing engine.
A general-purpose firewall sees SIP as just another UDP stream on port 5060. An SBC sees the INVITE, reads the headers, checks the rate, validates the source, and decides whether the call deserves to exist.
The practical value for enterprises in Metro Manila, Cebu, and Davao is significant. Organizations running Yeastar PBX systems can layer SBC functionality at the network edge to filter SIP traffic before it reaches the P-Series call processing engine. Enterprises with FortiGate firewalls gain an additional advantage: Fortinet’s application-layer inspection profiles can identify and block known SIP attack signatures at the perimeter, adding VoIP-specific threat intelligence to the existing firewall infrastructure.
Making Intrusion Detection Voice-Aware
Traditional network intrusion detection systems (IDS) were built for data protocols. They excel at spotting port scans, SQL injection attempts, and known malware signatures in HTTP traffic. Voice protocols present a different challenge: SIP sessions are stateful, call behavior follows predictable patterns, and the relevant metrics involve call duration, registration frequency, and codec negotiation sequences rather than payload signatures.
Researchers at multiple institutions have addressed this gap. A study on VoIP-aware network attack detection proposed detection schemes based on the statistics and behavior of SIP traffic, using 5-tuple information (source IP, source port, destination IP, destination port, and protocol) combined with call behavior baselines. The system establishes what normal SIP traffic looks like for a given network and flags deviations: a sudden spike in REGISTER requests from a single IP, an unusual number of failed authentication attempts, or INVITE floods targeting a specific extension range.
This kind of network intrusion detection for voice systems requires tuning. A BPO operation with 500 agents generates legitimate SIP traffic patterns that would look anomalous on a 30-extension office network. The baseline must match your actual environment. Enterprises that already practice structured network logging as part of their VoIP troubleshooting workflow have a head start here, because they’ve already collected the historical traffic data needed to establish those baselines.
VoIP security monitoring tools like VIAVI Observer extend this capability by providing real-time quality assurance for unified communication services, with accelerated root-cause analysis for both RTP and SIP traffic. When unified communications threat detection catches an anomaly, having the packet-level visibility to confirm whether it’s an actual attack or a misconfigured endpoint saves your team hours of investigation.
Encryption Finally Arrives in Production
For years, encryption was available in the SIP ecosystem but rarely deployed. SRTP (Secure Real-time Transport Protocol) encrypts the audio media stream. TLS (Transport Layer Security) encrypts the SIP signaling channel. Together, they prevent eavesdropping on call content and protect authentication credentials transmitted during SIP registration.
The barrier to adoption was always interoperability. If your PBX supports TLS but your SIP trunk provider doesn’t, the connection falls back to plaintext. If one endpoint supports SRTP but the other doesn’t, the call either fails or proceeds unencrypted. Philippine SIP trunk providers have been slow to mandate TLS, which means many enterprise deployments still run signaling in the clear even when their PBX hardware fully supports encryption.
The calculus is changing. The “Store Now, Decrypt Later” threat model assumes that adversaries are capturing encrypted traffic today with the expectation of breaking the encryption later using quantum computing advances. For enterprises handling sensitive data (healthcare, financial services, government agencies subject to DICT compliance requirements), enabling SRTP and TLS today is insurance against a future decryption capability that may be only years away. This is especially relevant for Philippine government agencies and hospitals, where compliance and security planning should account for the full lifecycle of captured traffic, not just its protection at the moment of transmission.
Tip: Check whether your SIP trunk provider supports TLS on their side. If they don’t, SRTP on the media path still protects the audio content, but your SIP credentials and call metadata remain visible to anyone capturing traffic between your PBX and the provider’s gateway. Push your provider to enable TLS, or evaluate alternatives that already support it.
Assembling the Architecture for Philippine Networks
Putting these layers together produces a defense-in-depth architecture with five tiers:
- Perimeter: SBC or SIP-aware firewall inspects all inbound SIP traffic, enforces rate limiting, performs topology hiding, and blocks known attack signatures. Geo-blocking restricts SIP registrations to Philippine IP ranges (and any specific international ranges your business requires).
- Network: Voice VLAN segmentation isolates SIP and RTP traffic. Inter-VLAN routing policies prevent data-side hosts from reaching voice endpoints directly. 802.1X port authentication ensures only authorized devices connect to voice switch ports.
- Detection: VoIP-aware IDS monitors SIP traffic statistics and call behavior against established baselines. Alerts trigger on registration anomalies, INVITE floods, and unusual call patterns. VoIP packet analysis captures provide the forensic detail needed to confirm and investigate incidents.
- Encryption: TLS secures SIP signaling between the PBX and SIP trunk provider. SRTP encrypts RTP media streams end-to-end between endpoints. Certificate management ensures TLS implementations use current, properly validated certificates.
- Access Control: Multi-factor authentication on PBX administration interfaces. Role-based access restricts configuration changes to authorized personnel. Firmware patching follows a documented schedule tied to vendor security advisories.
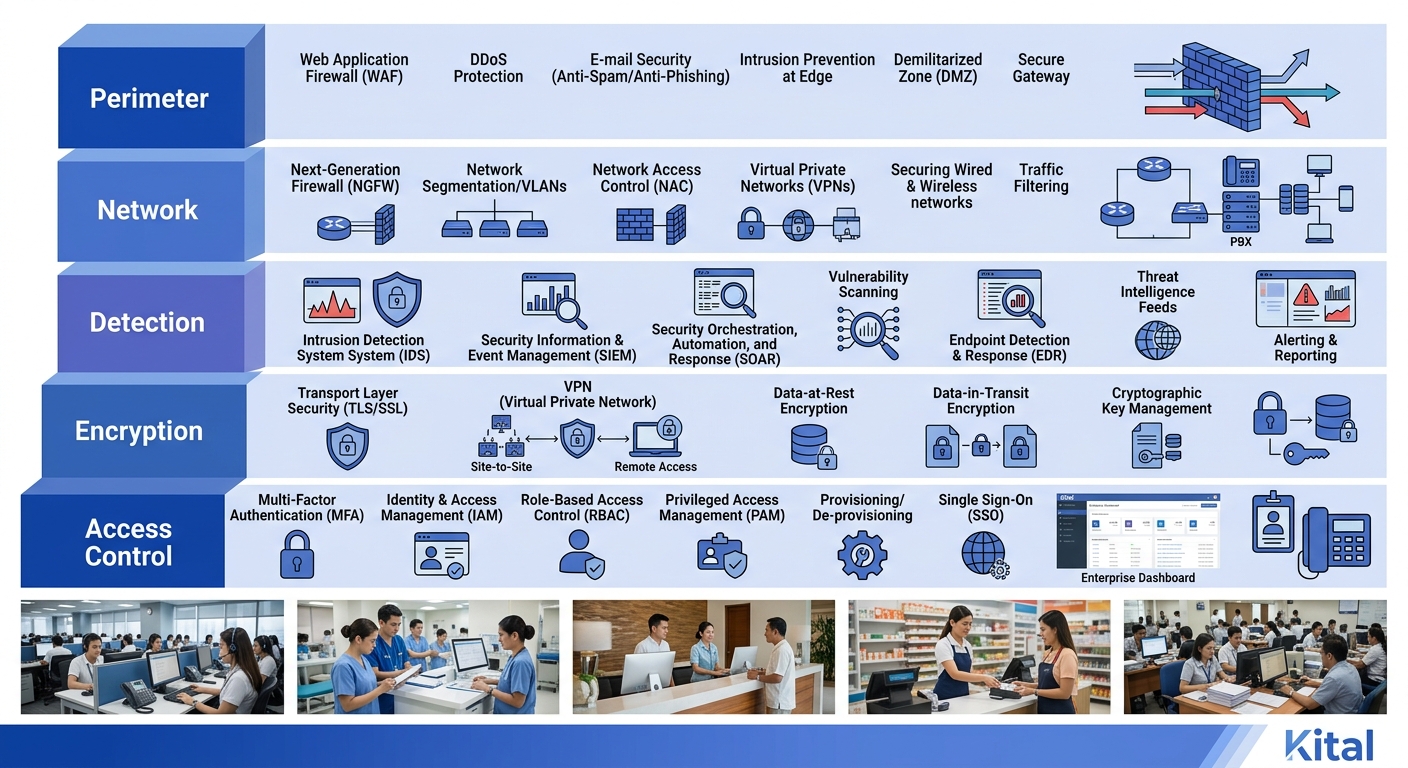
The cost and complexity of this architecture scale with organization size, but even a 50-seat office in Quezon City benefits from implementing the first three tiers. Voice VLAN segmentation costs nothing beyond switch configuration time. SBC functionality is included in many modern PBX platforms. And baseline SIP traffic monitoring can run on open-source tools if budget is tight.
For larger deployments (BPO operations, hospital networks, multi-branch enterprises), the full five-tier stack becomes essential. The volume of SIP traffic and the value of the communications being protected both justify the investment. Organizations already running a continuous VoIP performance benchmarking framework can integrate security metrics into the same monitoring pipeline, catching degradation that might indicate an active attack rather than a network performance issue.
The State of Play
The Philippine enterprise VoIP security landscape sits at an inflection point. Adoption of IP telephony has outpaced adoption of the security measures designed to protect it. Many organizations have voice VLANs configured but no SBC. Others have an SBC but no VoIP-specific intrusion detection. Encryption remains the weakest link, with TLS support on local SIP trunks still inconsistent.
The threat actors targeting these systems aren’t waiting. SIP protocol attacks continue to grow in sophistication, and the commoditization of attack tools means that even unsophisticated adversaries can launch registration floods or toll fraud campaigns with minimal effort. Philippine enterprises that treat VoIP security as an afterthought are building critical communications infrastructure on a foundation that’s already being actively undermined.
The defense architecture outlined here isn’t theoretical. Every component exists in production today, supported by vendors already active in the Philippine market. The question for most enterprises isn’t whether to implement these protections. It’s whether they’ll do it before their first significant incident forces the conversation.